Subscriber terminal Software version 2.4.7 (09.2022) |
|
Document version | Software | Release date | Changes |
|---|---|---|---|
| Version 1.1 | 2.4.7 | 09.2022 | Second publication |
Version 1.0 | 1.0.1 | 04.2021 | First publication |
GPON network belongs to one of the varieties of passive optical PON networks. This is one of the most modern and effective solutions for "last mile", which allows significant savings on cable infrastructure and provides data transmission speed of up to 2.5 Gbps downlink and 1.25 Gbps uplink. The use of GPON-based solutions in access networks makes it possible to provide end users with new IP services together with traditional ones.
The main advantage of GPON is the use of a single line terminal (OLT) for multiple subscriber devices (ONT). OLT is a converter of Gigabit Ethernet and GPON interfaces, which serves to connect the PON network with higher-level data transmission networks. The ONT device is designed to connect customers' equipment to broadband access services. It can be used in residential areas and business centers.
The user manual describes the purpose, main technical specifications, configuration rules and monitoring of the optical network terminal NTU-MD500P.
Notes and Warnings
The tips contain important information or recommendations for using and configuring the device. |
The notes contain additional information on using and configuring the device. |
Warnings inform of the situations when actions may harm the device or a user, lead to fault operation of the device or data loss. |
NTU-MD500P is an optical network terminal that has four 10/100/1000BASE-T ports with support for IEEE 802.3at PoE+ technology. NTU-MD500P provides up to 30 W of power on 10/100/1000BASE-T ports with a PoE power budget of 65 W.
Support for PoE technology allows NTU-MD500P to supply power via UTP cable to IP phones, wireless access points, IP cameras and other PoE-enabled devices.
The advantage of GPON technology is the optimum use of bandwidth. This technology is the next step to provide new high-speed internet connection at home and in offices. Designed to deploy a network inside a home or building, NTU-MD500P provides reliable connection with high bandwidth over long distances for users living and working in remote apartment buildings and business centers.
NTU-MD500P has the following interfaces:
NTU-MD500P supports the following functions:
L2TP over IPsec;
IPsec (trasport mode);
NAT (Network Address Translation);
The figure below shows the use case of NTU-MD500P.
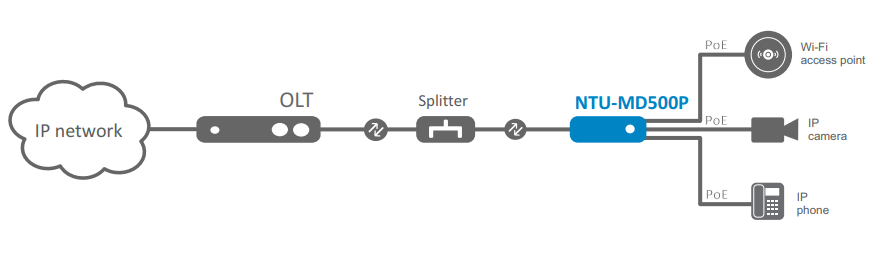
Figure 1 — NTU-MD500P use case
The main technical parameters of the terminal are given in Table 1:
Table 1 — Technical specifications
| Parameters of LAN Ethernet interfaces | |
Number of interfaces | 4 |
|---|---|
Electrical connector | RJ-45 |
Data rate | Auto-detection, 10/100/1000 Mbps, duplex/half duplex |
Supported standards | IEEE 802.3i 10BASE-T Ethernet |
| PON interface parameters | |
Number of interfaces | 1 |
| Supported standards | ITU-T G.984.x Gigabit-capable passive optical networks (GPON) |
| Connector type | SC/APC corresponds to ITU-T G.984.2, ITU-T G.984.5 Filter, FSAN Class B+, SFF-8472 |
| Transmission medium | Fiber optic cable SMF — 9/125, G.652 |
| Split ratio | Up to 1:128 |
| Maximum distance | 20 km |
| Transmitter: | 1310 nm |
| 1244 Mbps |
| From +0.5 dBm to +5 dBm |
| 1 nm |
| Receiver: | 1490 nm |
| 2488 Mbps |
| From -8 to -28, BER≤1.0x10-10 |
| Optical overload of the receiver | -8 dBm |
| Management | |
| Local management | Web, CLI |
| Remote control | TR-069, OMCI |
| Firmware update | OMCI, TR-069, HTTP, TFTP |
| Access restriction | By password |
| General parameters | |
| Power supply | 110-250 V AC, 50-60 Hz |
| Maximum power consumption | 80 W |
| Operating temperature range | From 0 to +40 °C |
| Relative humidity | No more than 80% |
| Dimensions (W × H × D) | 267 × 44 × 178 mm |
| Form factor | 19", size 1U |
| Weight | 1.56 kg |
This section describes design and indicators layout of the device. Images of the front, back and side panels of the device are shown in the section, connectors, LED indicators and controls are described.
NTU-MD500P is enclosed in a metal case suitable for 19” rack, the height of the case is 1U.
The device front panel layout is shown in Figure 2.
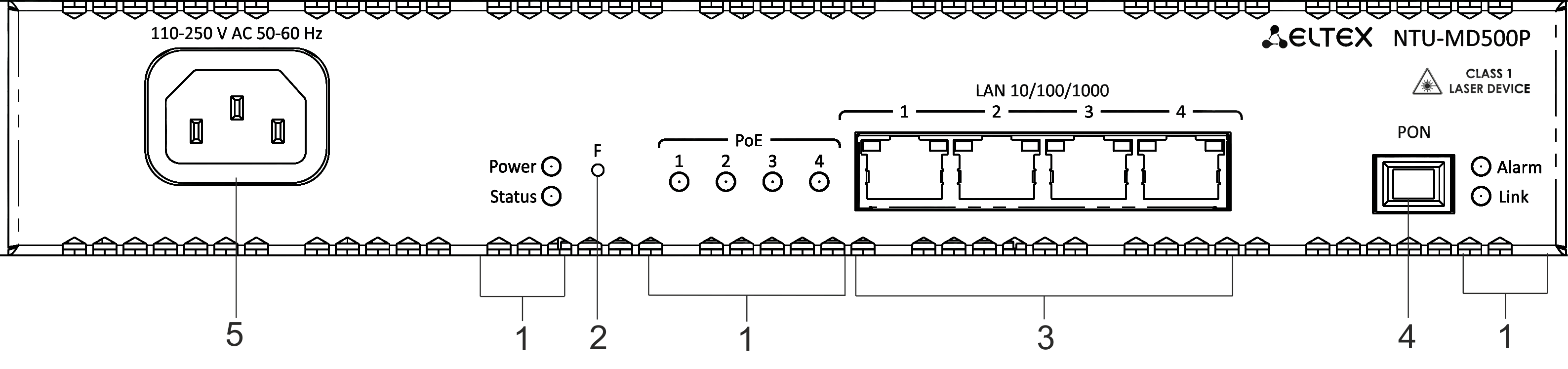
Figure 2 — NTU-MD500P front panel
Table 2 — Description of connectors and front panel controls
№ | Front panel element | Description | |
|---|---|---|---|
1 | Power | Device power indicator | |
Status | Device operation indicator | ||
Alarm | Indicator of optical signal absence | ||
Link | Indicator of optical interface operation | ||
PoE 1-4 | Status indicators of PoE ports | ||
2 | F | Functional button to restart the device and reset to factory settings: - pressing the button for less than 10 seconds restarts the device; - pressing the button for more than 10 seconds resets the device to the factory settings. | |
3 | LAN 10/100/1000 1..4 | 4 RJ-45 ports for connecting network devices | |
4 | PON | PON SC port (socket) of the GPON optical interface | |
5 | 110-250 V AC 50-60 Hz | Connector for AC power source | |
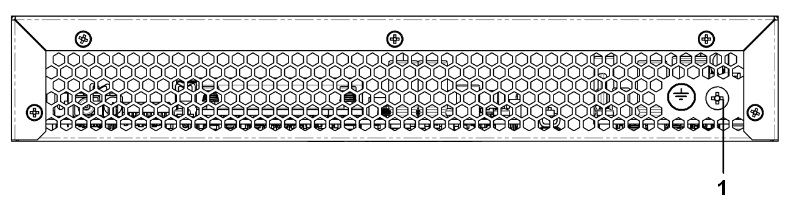
Figure 3 — NTU-MD500P back panel
№ | Back panel element | |
|---|---|---|
1 | Earth bonding point | |
Figure 4 — NTU-MD500P left-side panel
There are ventilation grilles on the side and back panels of the device, which serve to remove heat. Do not cover the ventilation grilles, it can lead to overheating of the device components and cause malfunctioning. See recommendations for device installation in the Installing and connecting NTU-MD500P section.
System indicators (Power, Status, Alarm, Link) are used to determine the operation status of the device nodes.
Table 3 — Light indication of device status
| Indicator name | Indicator status | Device status |
|---|---|---|
| Power | Solid green | The power is on, the device is operating normally |
| Off | The power is off | |
| Status | Solid red | The moment the drivers are lauching |
| Solid green | The device has a configuration which differs from the default one | |
| Green, flashing slowly | The default configuration is set on the device | |
| PoE 1-4 | Solid green | The PoE consumer is connected, the power supply is in on (the indicator corresponds to a port). |
Solid red | PoE error on port | |
Off | PoE consumer is not connected | |
| Alarm | Off | Normal operation of the device |
| Solid red | There is no optical signal | |
| Link | Off | The device is loading |
| Green, flashing fast | Getting settings via OMCI | |
| Solid green | The device has been successfully configured via OMCI. | |
| Green, flashing slowly | Configuration is absent (authorization) | |
| Red, flashing slowly | No signal from OLT | |
| LAN P1..P4 | Green | 10/100 Mbps connection has been established |
| Orange | 1000 Mbps connection has been established | |
| Flashing | The process of packet data transmission |
The basic delivery package of NTU-MD500P device includes:
This chapter describes procedure of installation into 19'' rack and connection to a power supply.
General requirements
When working with the device, it is necessary to comply with safety regulations for the operation with electrical installations.
It is forbidden to work with the device to persons who are not allowed to operation in accordance with the safety requirements. |
Electrical safety requirements
Before installing and switching on, it is necessary to check the device for visible mechanical damage. In case of damage, stop installing the device, draw up an appropriate report and contact the supplier. If the device has been exposed to low temperature for a long period of time, it should be kept at room temperature for two hours before operation. After a long stay of the device in high humidity conditions, it is necessary to keep it under normal conditions for at least 12 hours before switching on.
Mounting
The terminal package includes brackets for installation in a rack and screws for fixing brackets to the device case. To install the brackets:
Figure 5 — Mounting brackets
Installing into a rack
To install the device in a rack:
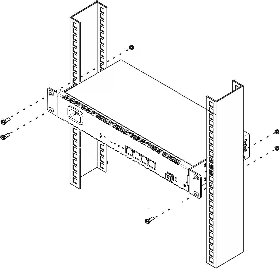
Figure 6 — Mounting brackets
The device has horizontal ventilation. Ventilation grilles are located on the side panels of the device. Do not cover the ventilation grilles to avoid overheating of the device components and malfunctioning.
To avoid overheating and provide the necessary ventilation, the device must be placed so that there is at least 10 cm of free space above and below it. |
1. Connect LAN port of NTU-MD500P and Ethernet port of your PC using an Ethernet cable.
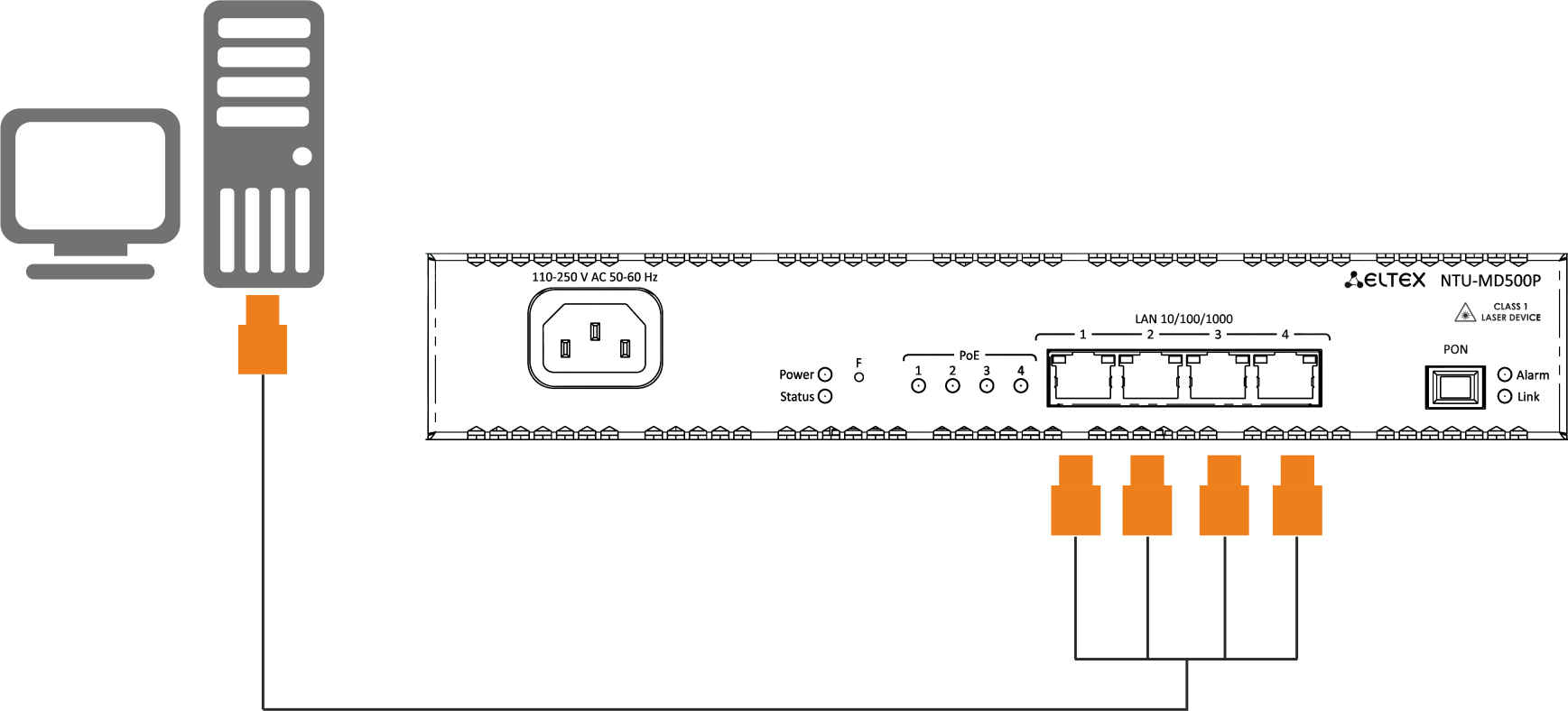
Figure 7 — Connecting the device to the computer
2. Connect the optical cable provided by the Internet service provider to the PON connector of the device.
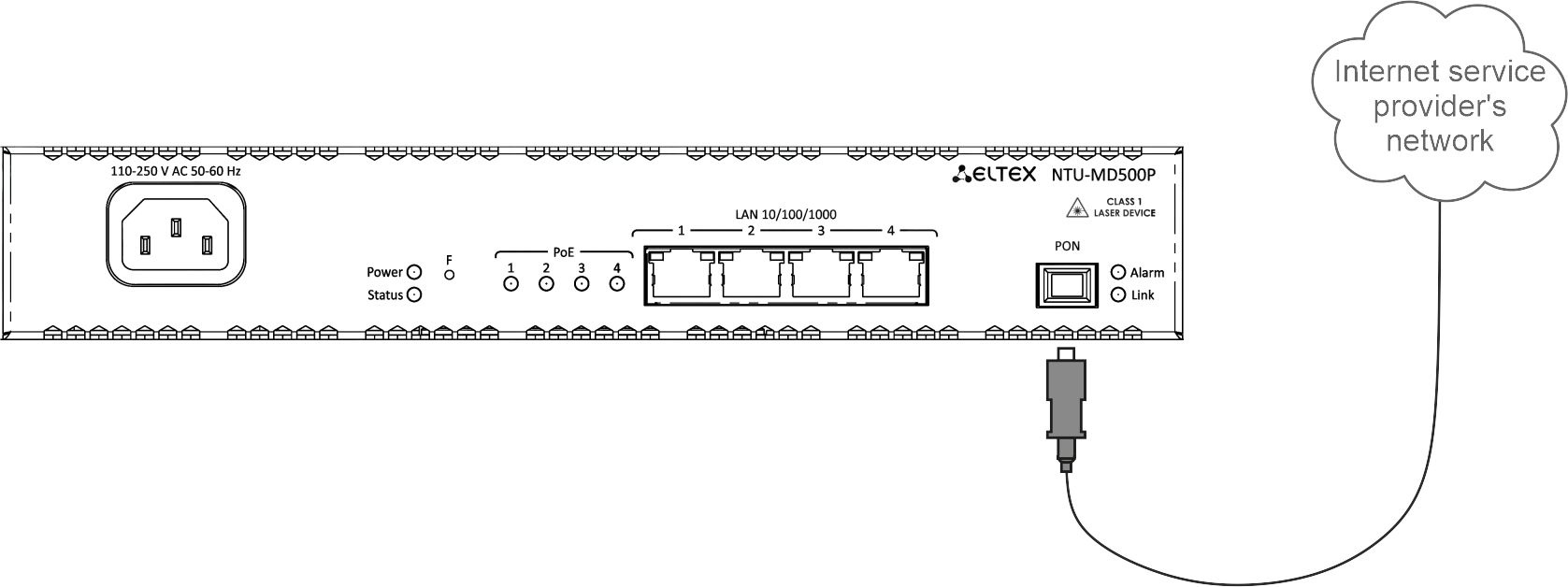
Figure 8 — Connecting the device to an Internet service provider's network
3. Connect the terminal to 220 V power supply network using the power adapter included into the delivery package. Wait until the device is fully loaded.
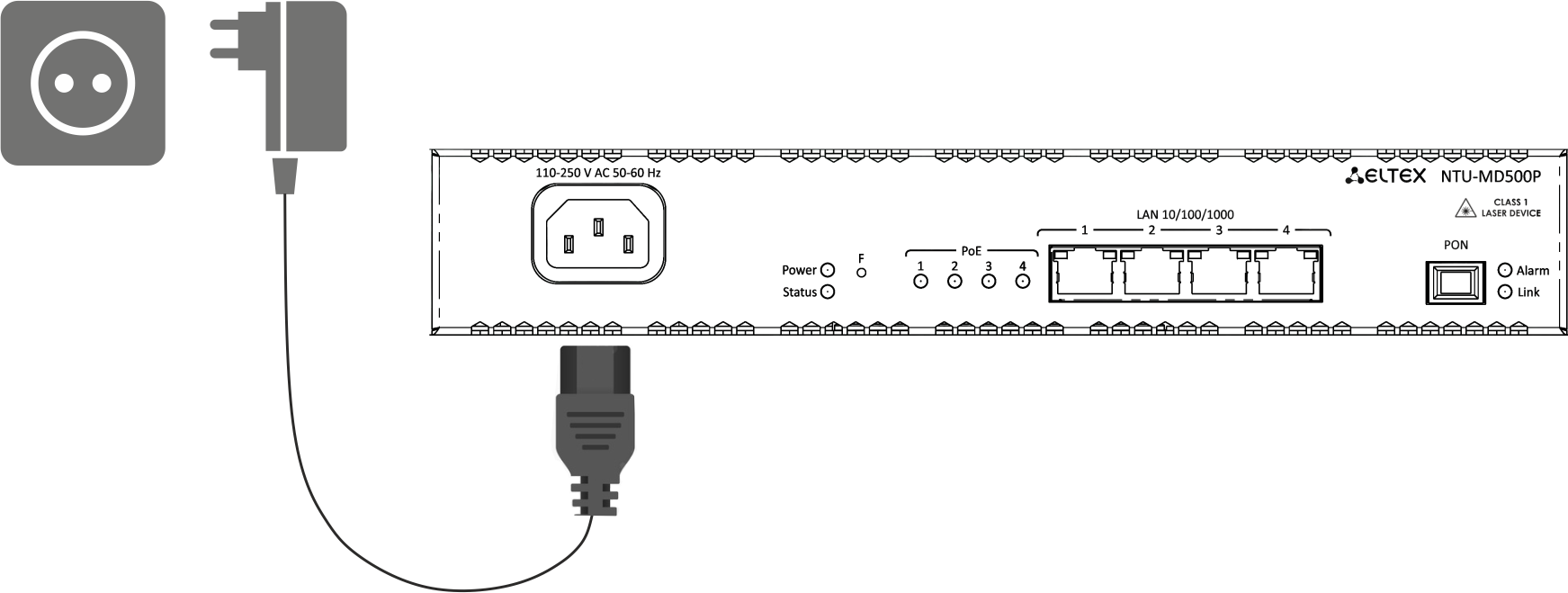
Figure 9 — Connecting the device to the power supply
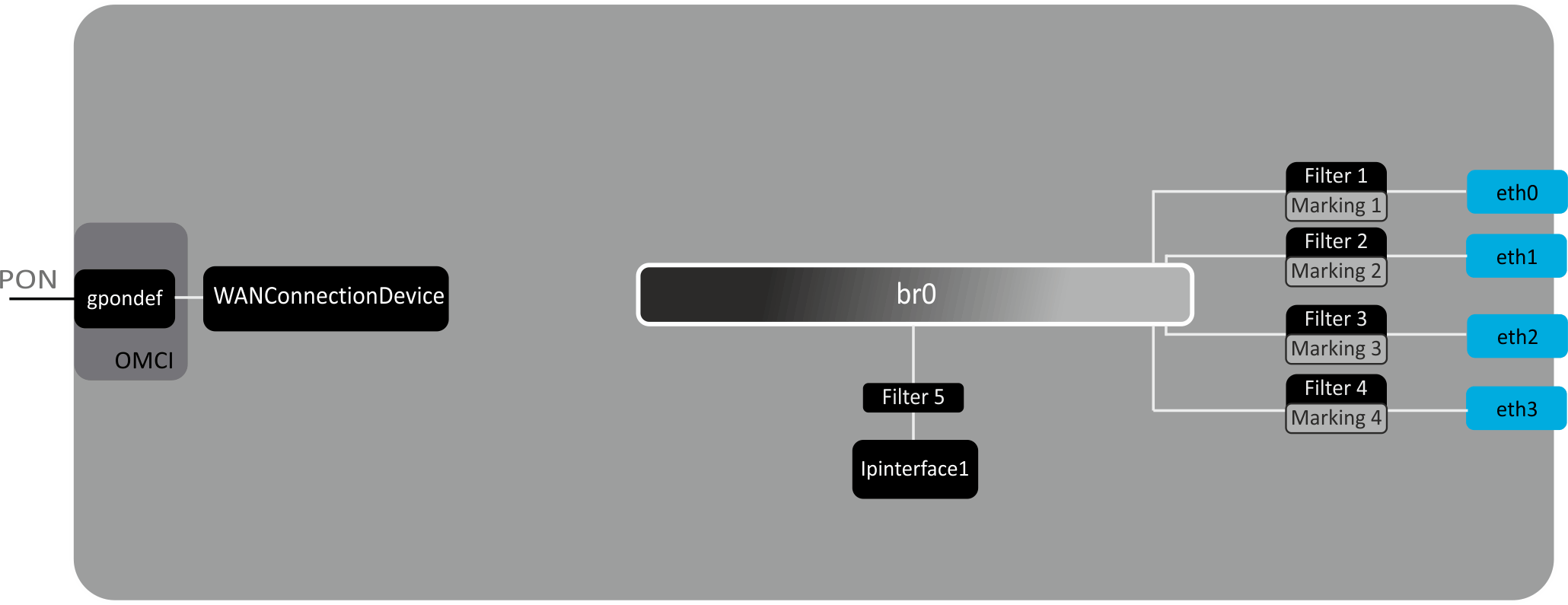
Figure 10 — Logical architecture of the device with the factory configuration
The main elements of the device:
In the factory configuration, the following logic blocks are present (Figure 10):
The br0 block in this case is intended for combining LAN ports into one group.
The eth0..3 blocks are physically Ethernet ports with an RJ-45 connector for connecting a PC, STB or other network devices. Logically included in the br0 block.
The Filter and Marking blocks are designed to put local interfaces in one group (in the br0 block). These blocks are responsible for the traffic transmission rules, the Filter blocks are responsible for incoming traffic on the interface, the Marking blocks are responsible for outgoing traffic.
The ipinterface1 block is a logical object where IP address for access to the local network is stored, as well as a DHCP server that distributes addresses to clients.
Getting started
To configure the device, you need to connect the device via a web browser:
Type the device IP address in the browser's address bar
The default IP address: 192.168.0.1, subnet mask: 255.255.255.0 |
If the connection is successful, a page with the authorization request will be displayed in the browser window: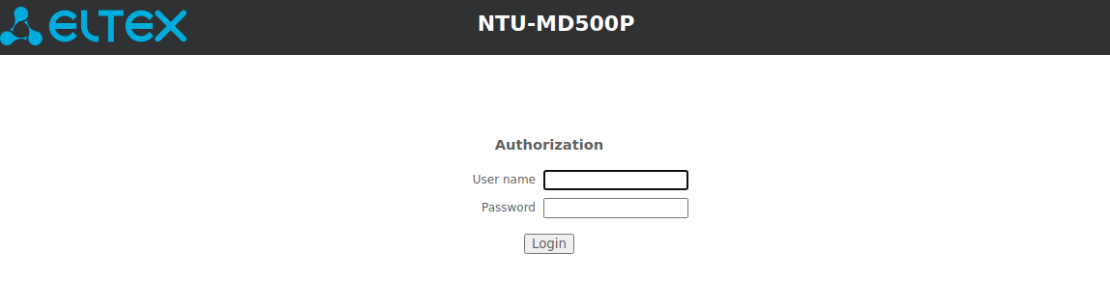
Enter username and password
Default user name — admin, password — password. |
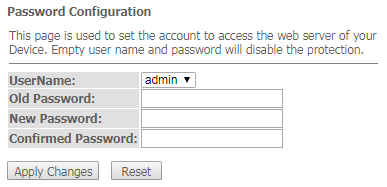
Changing the password
In order to avoid unauthorized access, it is recommended to change the password for further operation. To change the password in the menu Admin, section "Password", in the field "Old Password" enter the current password in the fields "New Password" and "Confirm new password" enter a new password. To save changes, click the Apply Changes button.
Elements of the web interface
General view of the device configuration window is shown below.
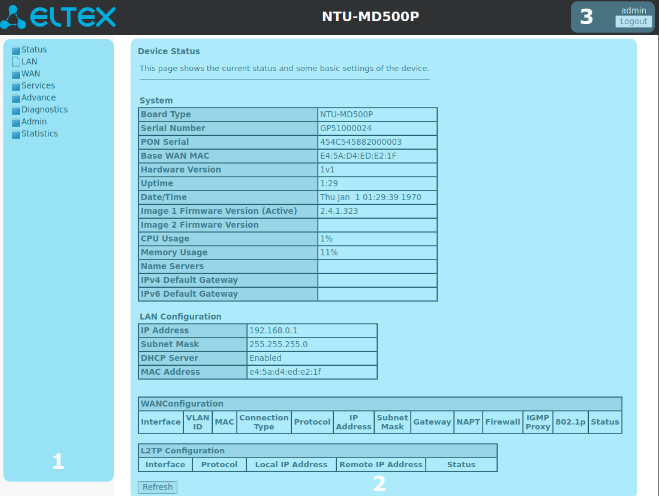
The user interface can be divided into 3 parts :
The section displays general information on the device, the main parameters of LAN and WAN interfaces.
Status → Device
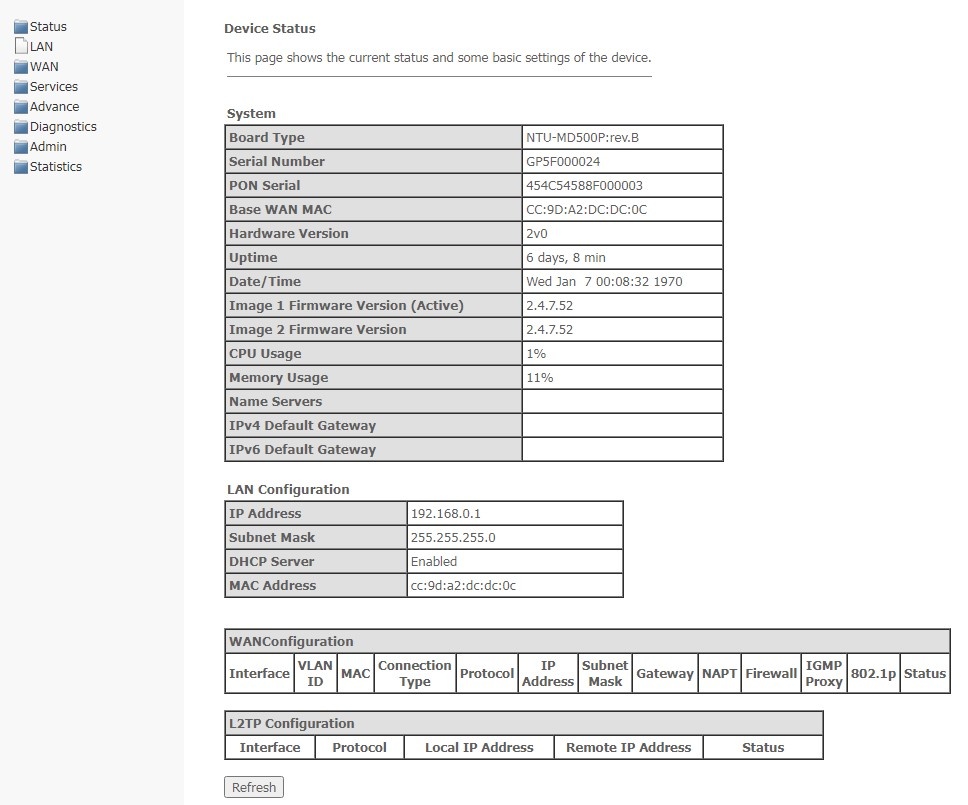
System
Board Type — hardware model;
Serial Number — serial number of the device;
PON Serial — serial number of the device in PON network;
Base WAN MAC — WAN MAC address of the device;
Hardware Version — hardware version of the device;
Uptime — device operation time;
Date/Time — the current time on the device;
Image 1 Firmware Version (Active) — current firmware version;
Image 2 Firmware Version — backup software version;
CPU Usage — percentage of CPU usage;
Memory Usage — percentage of memory usage;
Name Servers — name of DNS server;
IPv4 Default Gateway;
IPv6 Default Gateway.
LAN Configuration
IP Address — IP address of the device;
Subnet Mask — network mask of the device;
DHCP Server — status of DHCP server;
MAC Address — MAC address of the device.
WAN Configuration
L2TP Configuration
To update the data on the page, click Refresh.
The section displays the current status of the IPv6 system.
Status → IPv6
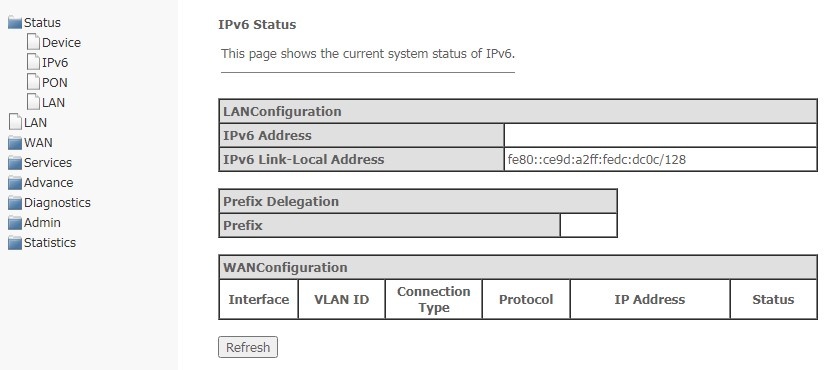
LAN Configuration
IPv6 Address;
IPv6 Link-Local Address — local IPv6 address.
Prefix Delegation
WAN Configuration
To update the data on the page, click Refresh.
The section shows the current state of the PON interface.
Status → PON
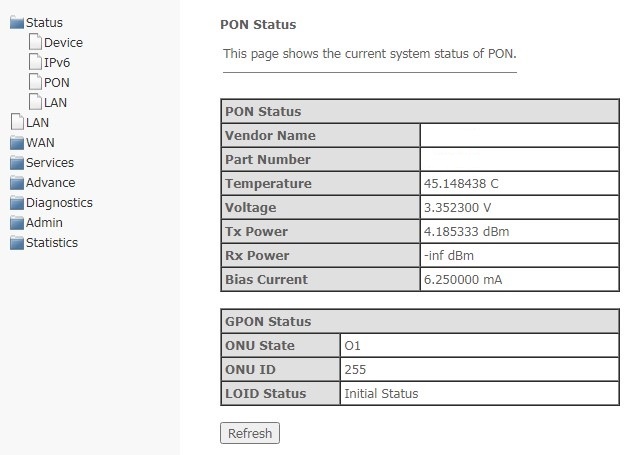
PON Status
GPON Status
To update the data on the page, click Refresh.
In this section, you can view the main parameters of LAN interfaces.
Status → LAN
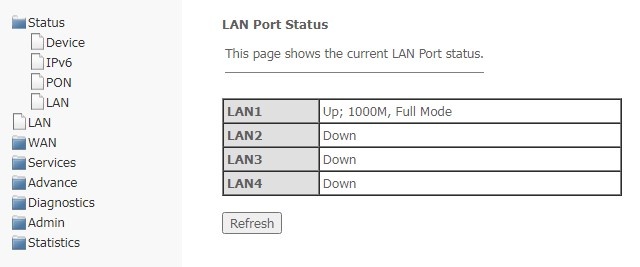
To update information in the table, click Refresh.
In this section, you can configure the main characteristics of wired and wireless LAN interfaces.
LAN
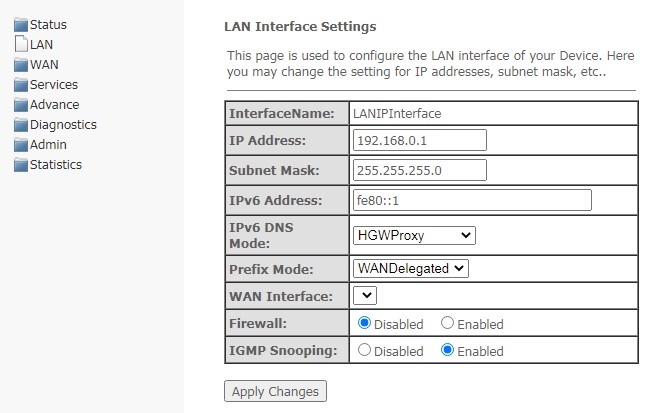
WANConnection — use the WAN interface to get the DNS server address;
Static — specify a static DNS server address (IPv6 DNS1, IPv6 DNS2).
To save changes, click Apply Changes.
In this section, you can configure the PON WAN parameters.
WAN → PON WAN
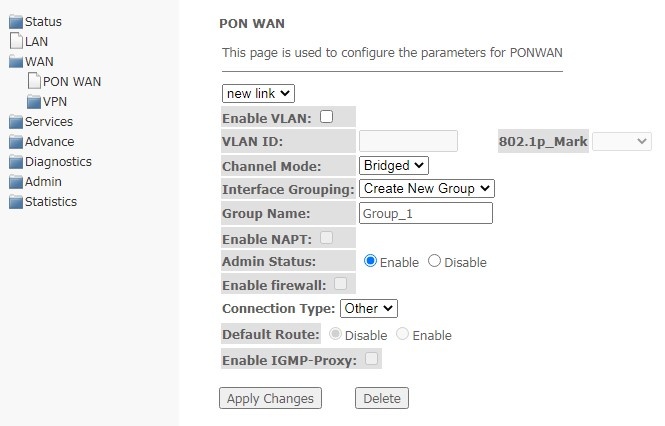
To save changes, click Apply Changes, to delete — Delete.
In this section, you can configure the virtual connection parameters L2TP VPN. The L2TP protocol is used to create a secure connection channel over the Internet between a remote user's computer and a local computer.
WAN → VPN → L2TP
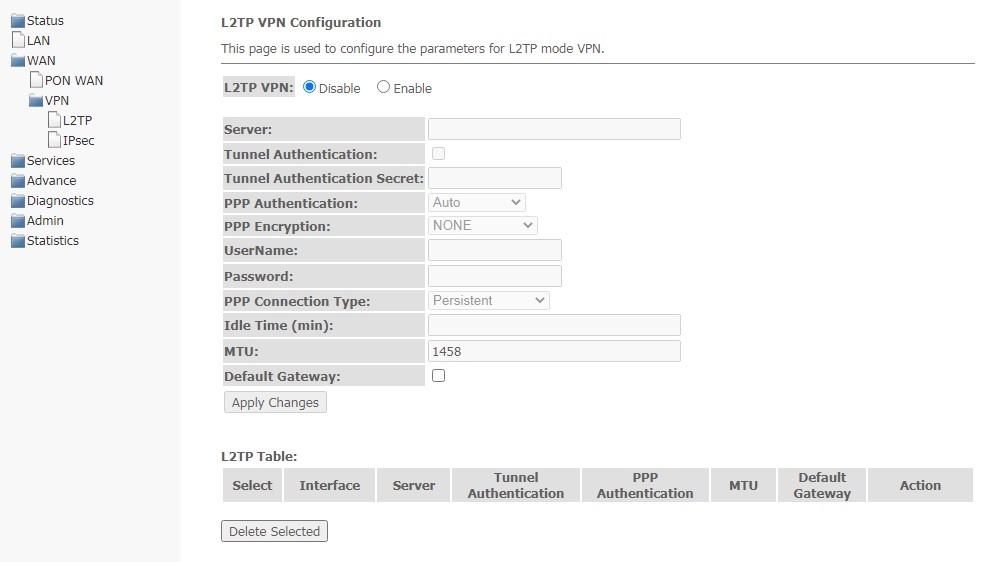
L2TP VPN is a mode in which access to the Internet is carried out through a tunnel using the L2TP protocol. When Enable is selected, the following parameters will be available for editing:
To save changes, click Apply Changes.
In the L2TP Table, you may view the status of a virtual L2TP VPN connection. To delete a certain entry, select the position and click Delete Selected.
This page is used to configure settings for VPN in IPsec mode.
WAN → VPN → IPsec
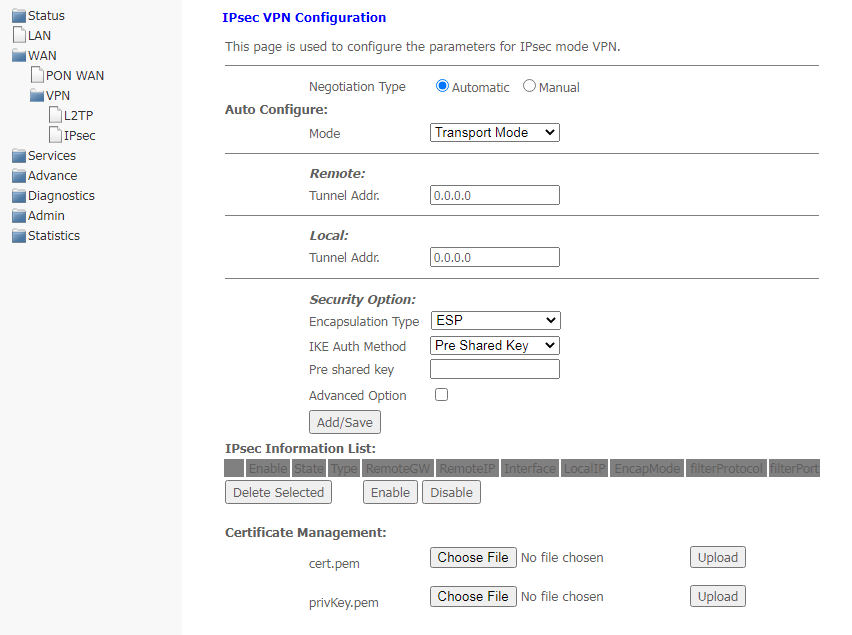
To save changes, click Add/Save.
In the table IPsec Information List, you can view, enable, disable and delete (Delete Selected) the created rules.
In this section, a DHCP server or a DHCP repeater is configured.
Services → DHCP (DHCP Server is selected)
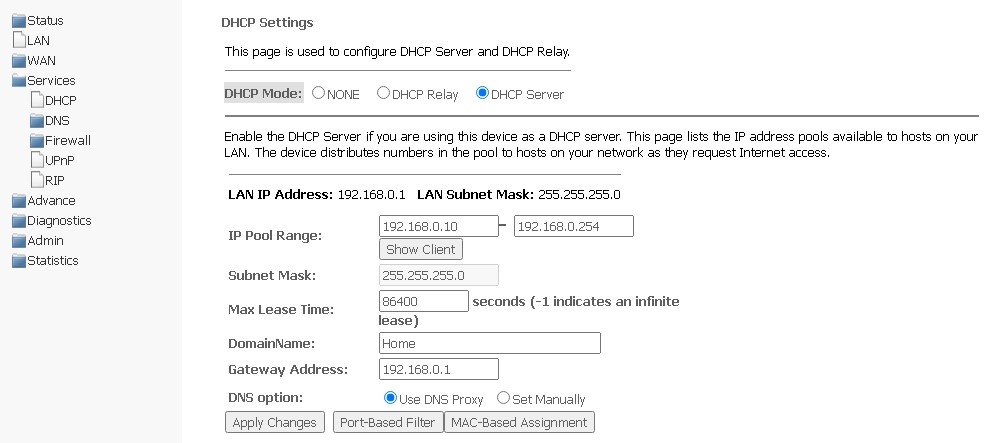
To save changes, click Apply Changes.
Port-Based Filter configures filtering according to ports, MAC-Based Assignment — according to MAC addresses.
Services → DHCP (DHCP Relay is selected)
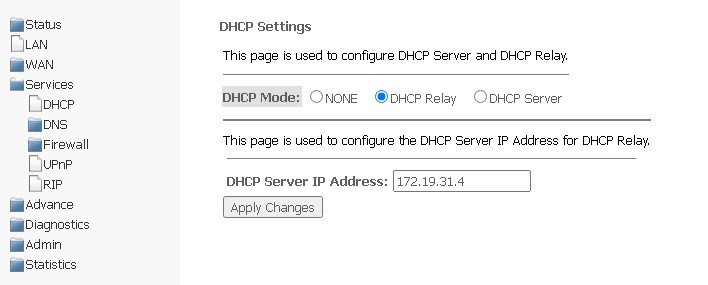
To save changes, click Apply Changes.
Dynamic DNS (dynamic domain name system) allows updating information on DNS server in real time and (optionally) in automatic mode. It is used to assign a permanent domain name to a device (computer, router, for example NTU-RG) having dynamic IP address. IP address might be obtained via IPCP in PPP connections or via DHCP.
Dynamic DNS is often used in local networks, where clients receive an IP address via DHCP, and then register their names in the local DNS server.
Services → DNS → Dynamic DNS
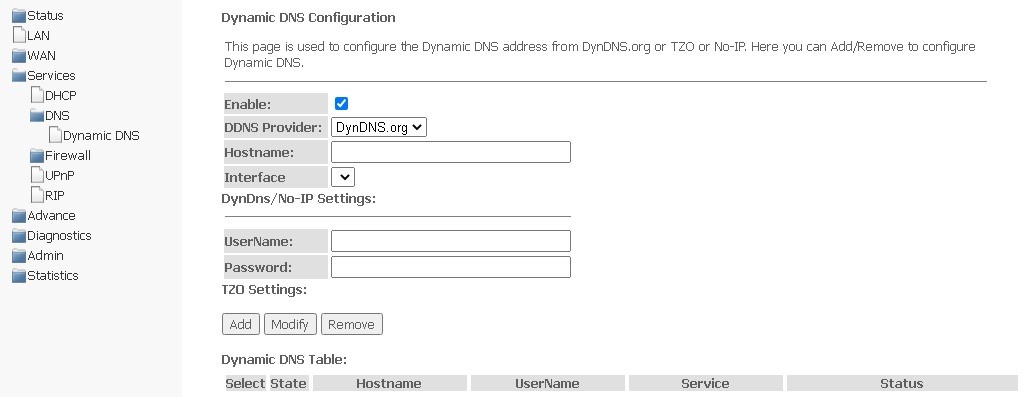
DynDns/No-IP Settings:
The section displays Dynamic DNS Table with a list of available DNS and its parameters. To add an entry, click Add. To change/delete a position, select it and click Modify or Remove.
In this section, you can enable or disable ALG and Pass Through services.
Services → Firewall → ALG
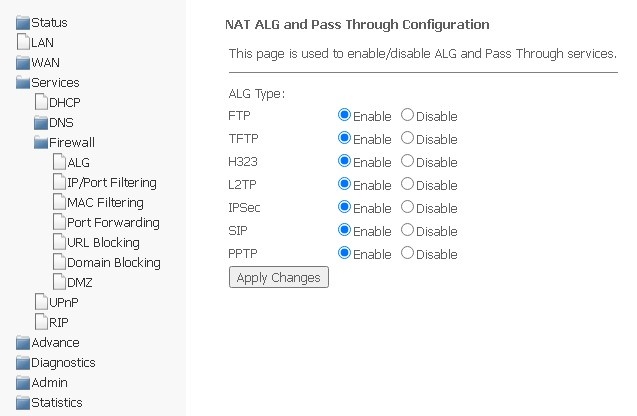
Please, do not forget to click Apply changes, to save changes made.
Address filtering settings are available in this menu. The IP filtering function allows you to filter traffic passing through the router according to IP addresses and ports. The use of such filters can be useful to protect or put restrictions on the local network.
Services → Firewall → IP/Port Filtering
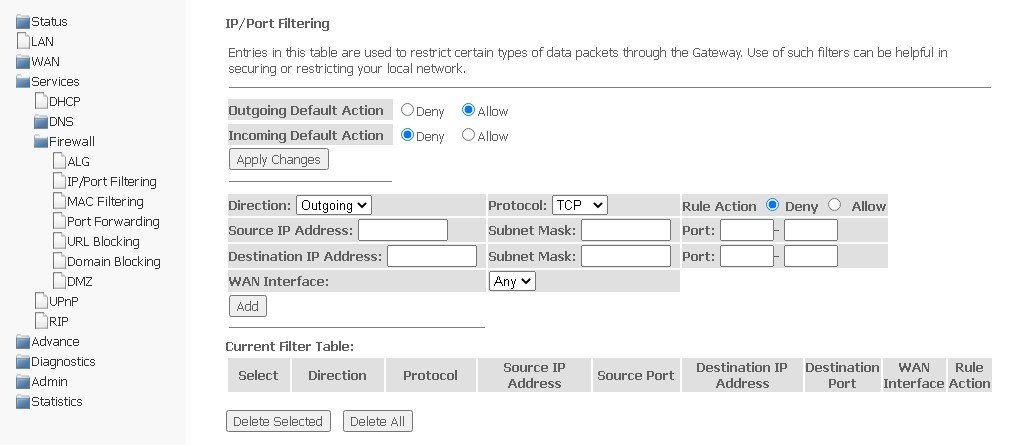
Default settings
To save changes made, click Apply Changes.
To add a filter, complete the appropriate fields and click Add:
The added filters are displayed in Current Filter Table. The entries in this table are used to restrict certain types of data packets through the gateway. To delete a certain filter, select an entry and click the Delete selected button, to delete all filters — Delete All.
The section helps to configure filtration based on MAC addresses, which allows you to forward or block traffic according to MAC address of the source and recipient.
Services → Firewall → MAC Filtering
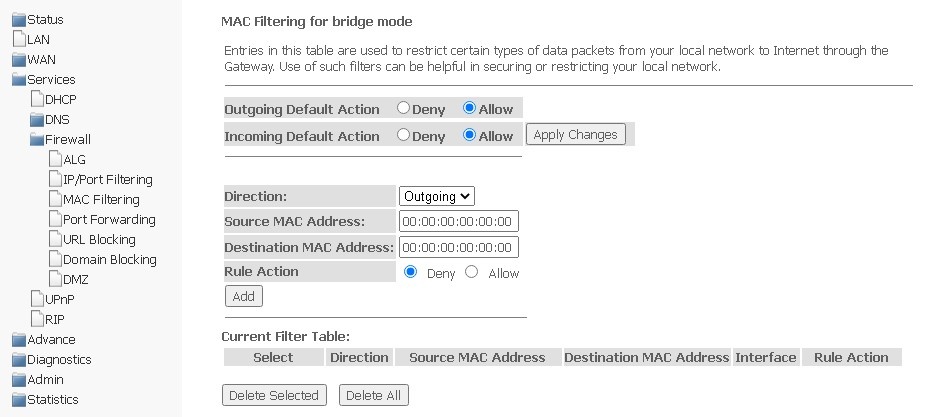
To save changes, click Apply Changes.
To add a filter, complete the appropriate fields and click Add button:
The added filters are displayed in the filter table below — Current Filter Table. The Rule action field displays the type of rule created (Allow or Deny traffic transmission). To delete a certain rule in the list, select it and click Delete Selected, to delete the entire list, click Delete All.
This section contains Current Port Forwarding Table displaying information on port forwarding. Entries in this table allow you to automatically redirect shared network services to a specific computer behind the NAT firewall. These settings are only necessary if you want to deploy a host, such as a web server or mail server, on a private LAN behind the NAT firewall of the router you are using. To save changes, click Apply Changes.
Services → Firewall → Port Forwarding 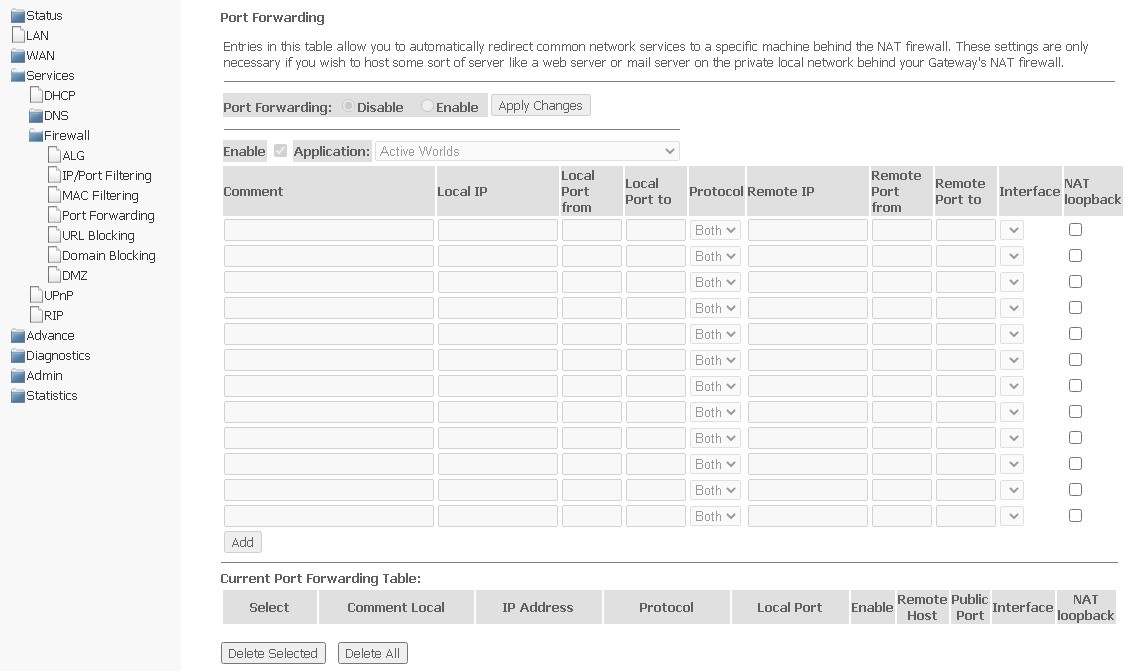
To add an entry to Current Port Forwarding Table, select Enable and complete the appropriate fields:
After completing the fields to add an entry, click Add. To delete a certain entry, select it and click the Delete Selected button, to delete the entire table — Delete All.
The URL filter performs full analysis and control for access to certain Internet resources. In this section you may set and view a list of prohibited/allowed URLs to visit. Here you can add a prohibited/permitted FQDN (Fully Qualified Domain Name) with the Add button, keyword filtering is also possible. The added restrictions are displayed in URL Blocking Table and Keyword Filtering Table, to delete a specific URL or keyword from the table, click on it, and then on the Delete Selected button. To remove all restrictions, click Delete All.
Services → Firewall → URL Blocking
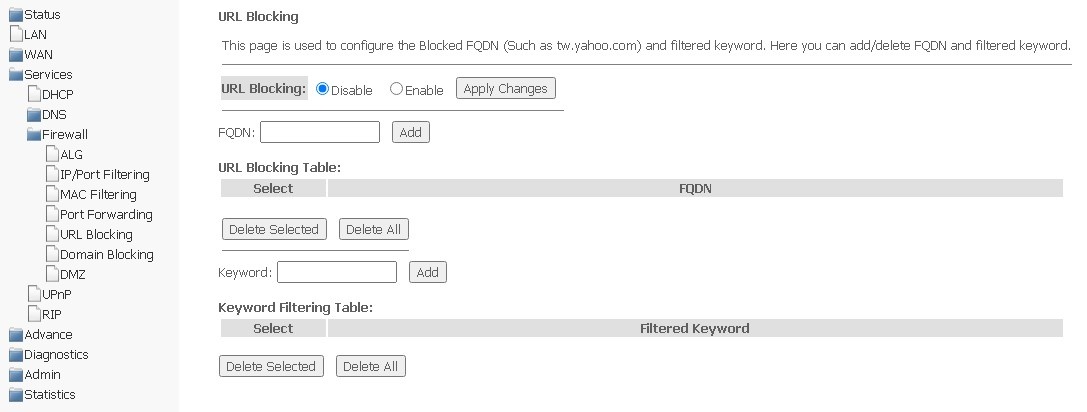
To save changes, click Apply Changes.
This section is used to specify domain blocking.
Services → Firewall → Domain blocking
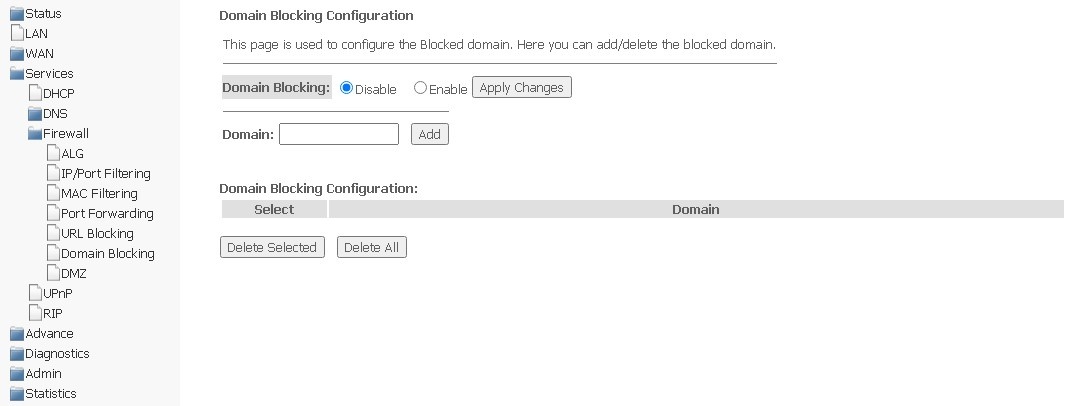
To block a domain, select Enable, complete the Domain field and click the Add button.
To save changes, use the Apply Changes button. All blocked domains are listed in the Domain Blocking Configuration table, to remove the block for a certain domain, select it and click Delete Selected, to remove all restrictions, click Delete All.
When setting IP address in the DMZ Host IP Address field, all requests from the external network that do not meet the Port Forwarding rules will be sent to the DMZ host (a trusted host with the specified address located in the local network).
Services → Firewall → DMZ
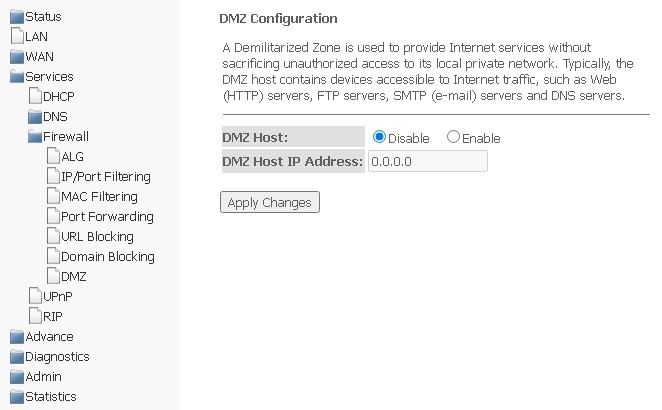
To save changes, click the Apply Changes button.
In this section, you may configure the Universal Plug and Play (UPnP) function. UPnP provides compatibility with network equipment, software, and peripherals.
Services → UPnP
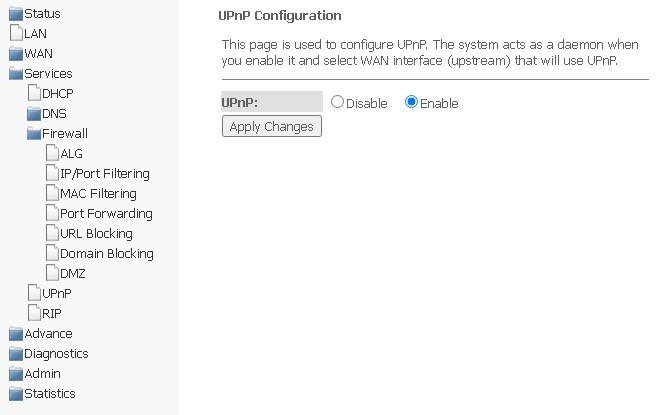
To use UPnP, you need to configure NAT on the active WAN interface. |
To save settings, click Apply Changes.
In this section you may select interfaces on devices that will use RIP and its version. Enable RIP if you are using this device as a RIP-enabled device to communicate with other users using the RIP Dynamic Routing protocol.
Services → RIP
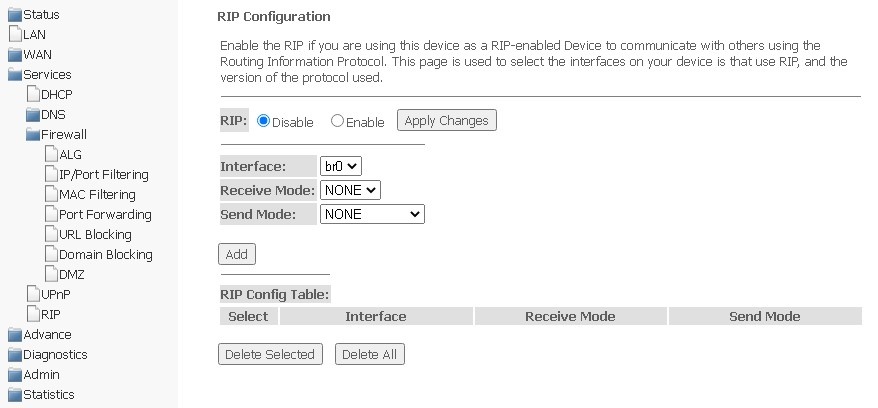
To accept and save settings, click Apply Changes.
RIP-enabled interfaces are displayed in RIP Config Table. To delete all entries in the table, click Delete All, to delete a certain entry from the list, select it and click Delete Selected.
The section displays a table of learned MAC addresses. The efficiency of ARP operation largely depends on the ARP cache, which is present on each host. The cache contains Internet addresses and their corresponding hardware addresses. The lifetime of each entry in the cache is 5 minutes from the moment the entry was created.
Advance → ARP table
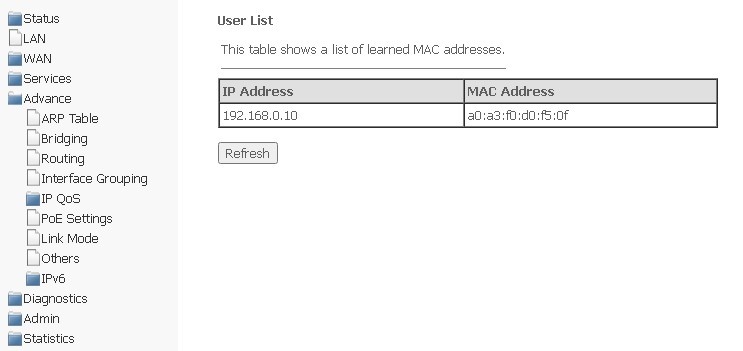
To update information in the table, click Refresh.
In this section, you may configure bridge parameters. Here you can configure the lifetime of addresses in the MAC table, as well as enable/disable the 802.1d Spanning Tree protocol.
Advance → Bridging
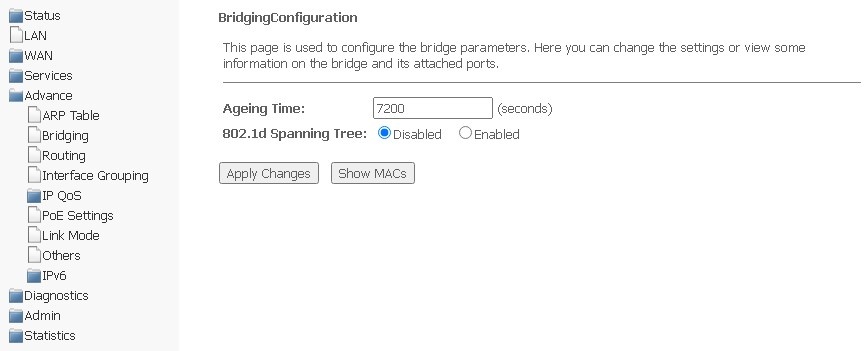
To save changes, click Apply Changes.
To view information on the bridge and its connected ports, click Show MACs.
Advance → Bridging → Show MACs
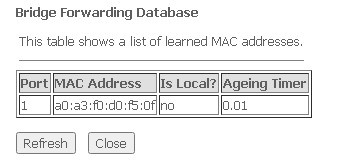
To update information in the table, click Refresh, to close — Close.
The section is used to configure static routing.
Advance → Routing
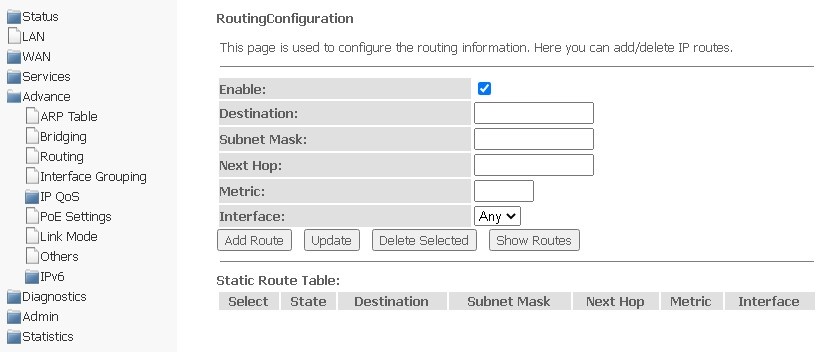
To add a static route, select Enable, complete the appropriate fields and click Add Route.
Added static routes are displayed in Static Route Table. To update the information in the table, click Update, to delete an entry from the table, select it and click Delete Selected.
To view the routes that the device frequently accesses, click Show Routes, then IP Route Table will be displayed.
Advance → Routing → Show Routes
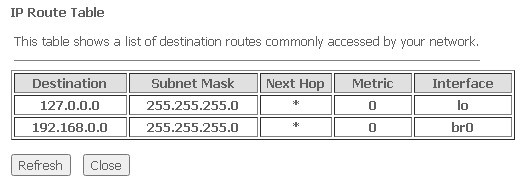
To update information in the table, click Refresh, to close it, click Close.
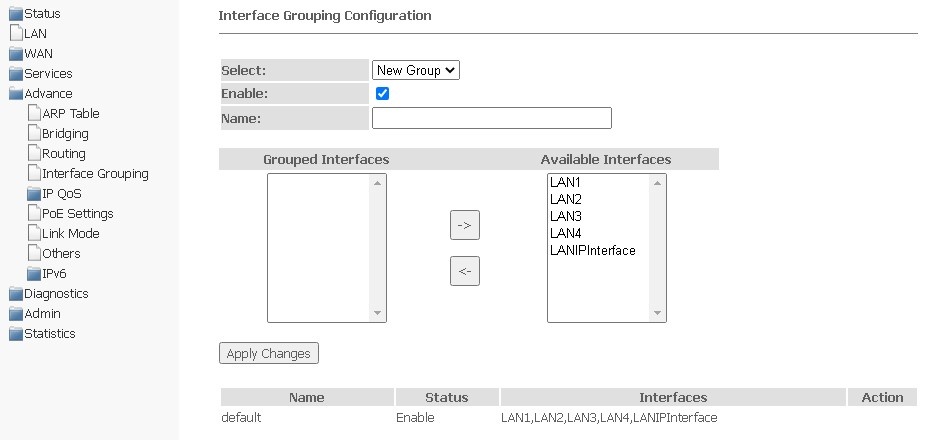
In this section, you can combine interfaces into different groups. By default, all interfaces are in the same group. To transfer the interface to a new group, you should:
Advance → Interface grouping
In this section, you can configure QoS queue policies for traffic processing.
Advance → IP QoS → QoS Policy
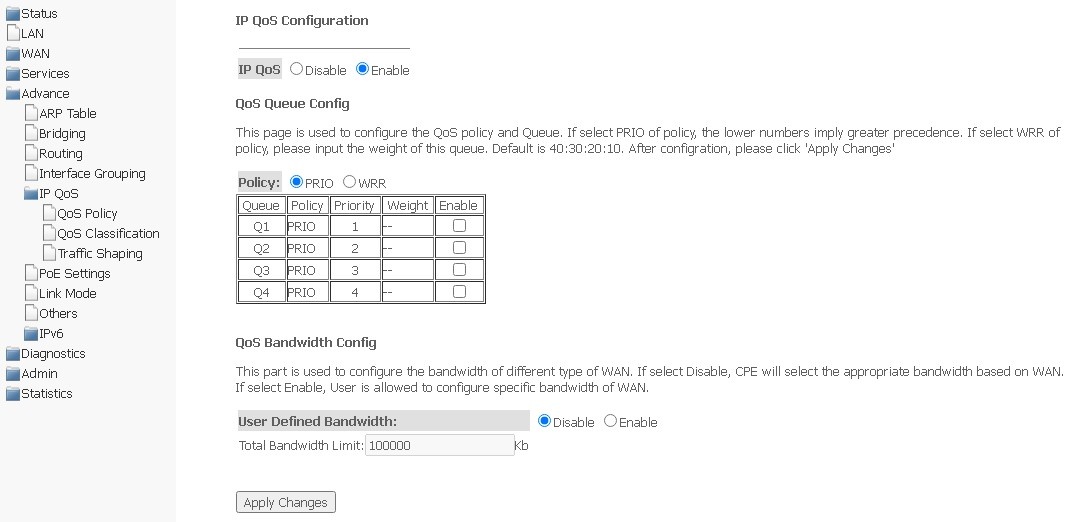
QoS Bandwidth Config
Is used to configure the bandwidth of individual services.
To save changes, click Apply Changes.
On this page, you can specify according to which fields and their values the packet will be classified, as well as which hardware queue it will eventually belong to.
Advance → IP QoS → QoS Classification
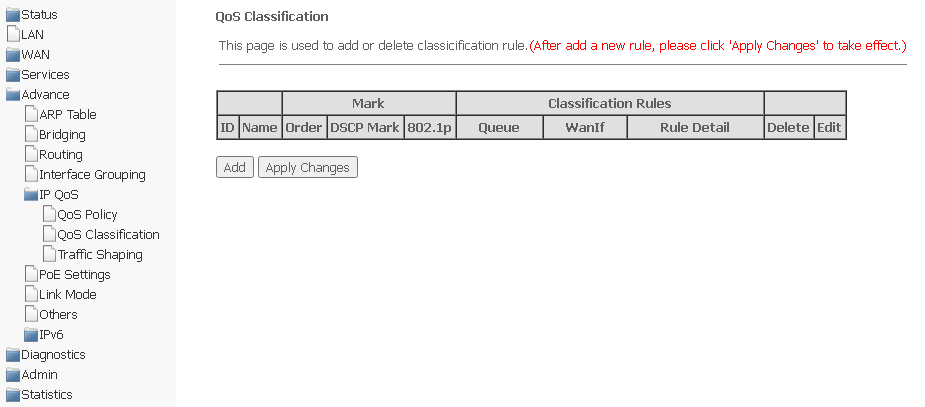
To add a rule, click Add and complete the appropriate fields.
Advance → IP QoS → QoS Classification → Add
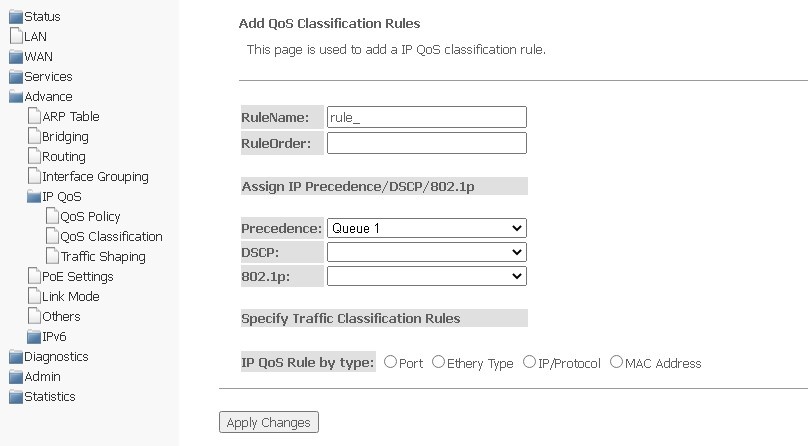
Assing IP Precedence/DSCP/802.1p — setting up the assignment of IP fields.
Specify Traffic Classification Rules — select traffic classification rule.
To save changes, click Apply Changes.
In this section, you can specify traffic restrictions according to certain rules.
Advance → IP QoS → Traffic Shaping
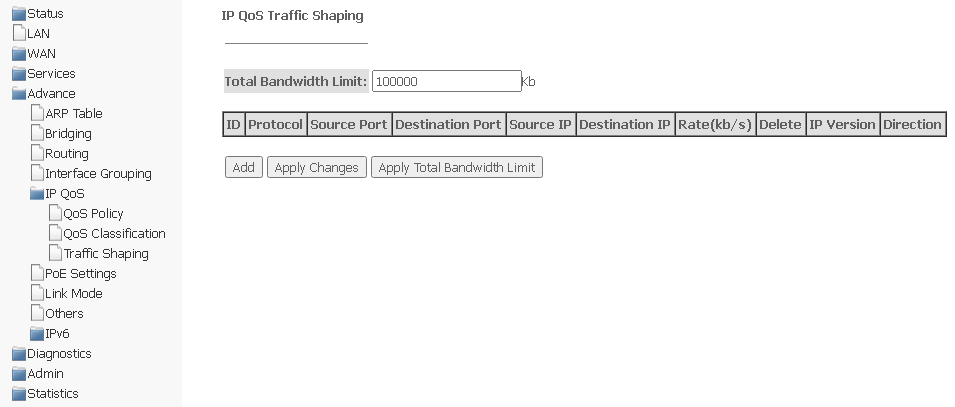
Total Bandwidth Limit (kb) — total bandwidth limit, kbit.
To add, click Add and complete the appropriate fields.
Advance → IP QoS → Traffic Shaping → Add
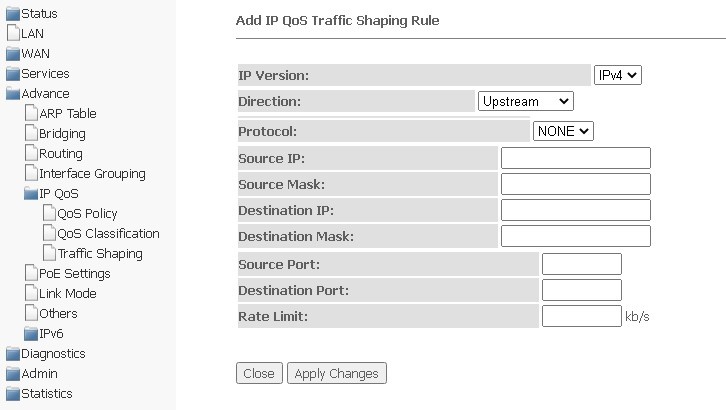
To save the changes, click Apply Changes, to cancel, click Close.
This page is used to configure PoE settings. Here, you can enable/disable PoE on LAN ports; to do this, you need to select Enable or Disable.
Advance → PoE Settings
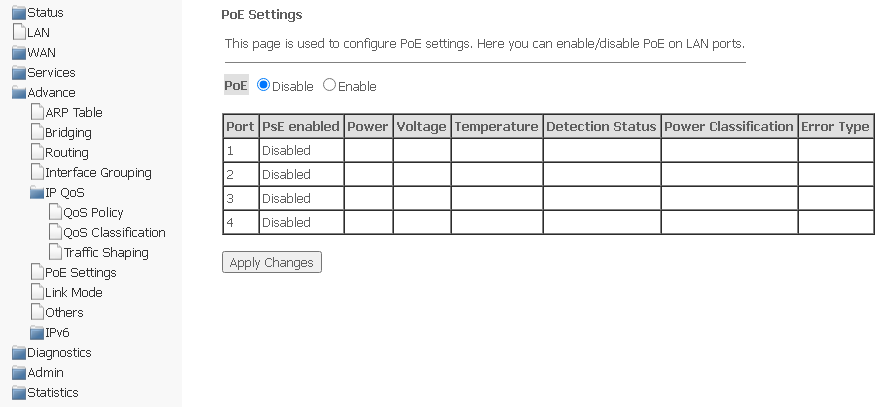
To save changes, click Apply Changes.
In this section, you can set the mode of LAN ports operation. LAN1/2/3/4 fields are used to set up the operation mode. Available modes are 10M Half Mode, 10M Full Mode, 100M Half Mode, 100M Full Mode and Auto Mode (auto detection mode).
Advance → Link mode
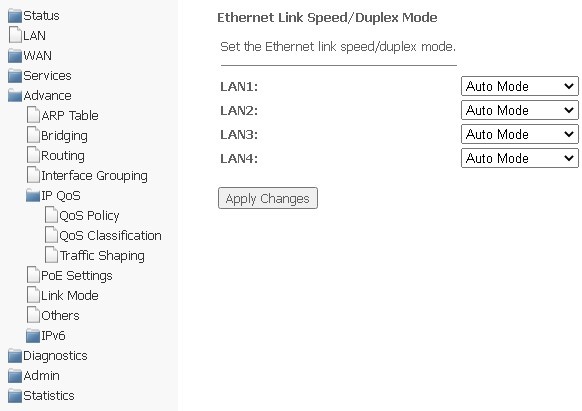
To save changes, click Apply Changes.
In this section, you can configure end-to-end IP transmission for WAN interfaces, as well as enable/disable JumboFrame transmission.
Advance → Others
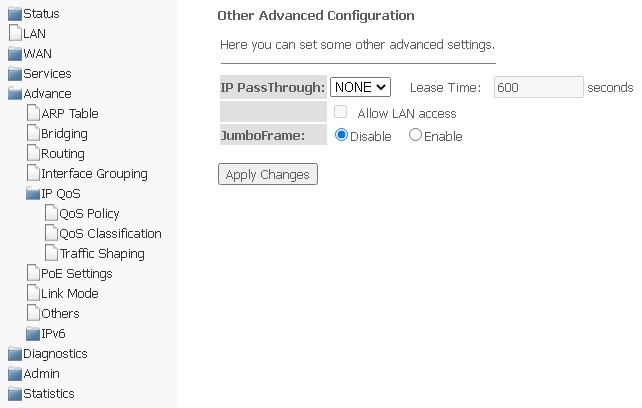
To save changes, click Apply Changes.
In this section, you can enable/disable IPv6; to do this, select Enable or Disable.
Advance → IPv6
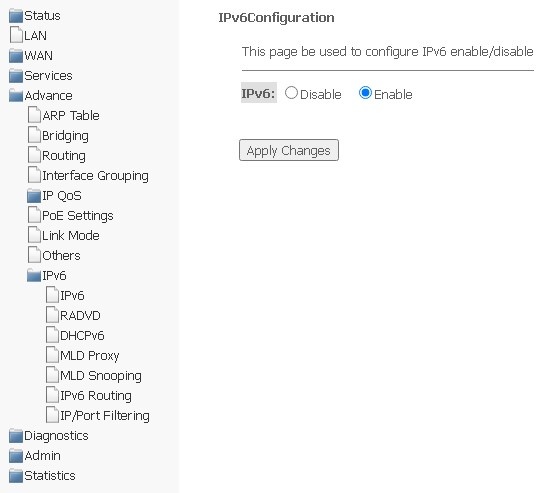
To save changes, click Apply Changes.
The section is used to configure RADVD (Router Advertisement Daemon).
Advance → IPv6 → RADVD
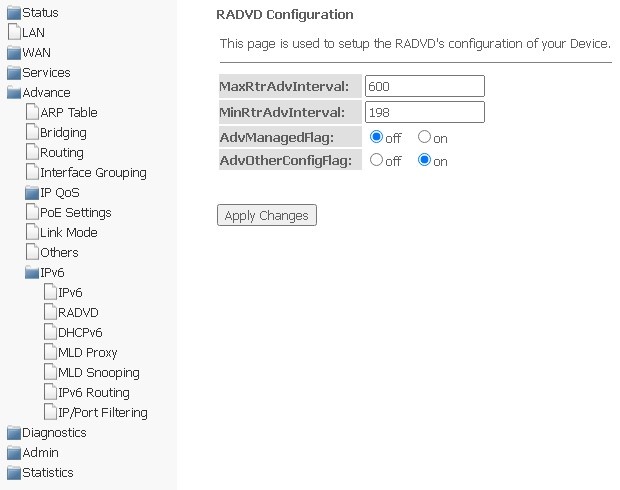
To save changes, click Apply Changes.
The section is used to configure DHCPv6 server. By default, it works in auto-configuration mode (DHCPServer(Auto)) via prefix delegation.
Advance → IPv6 → DHCPv6
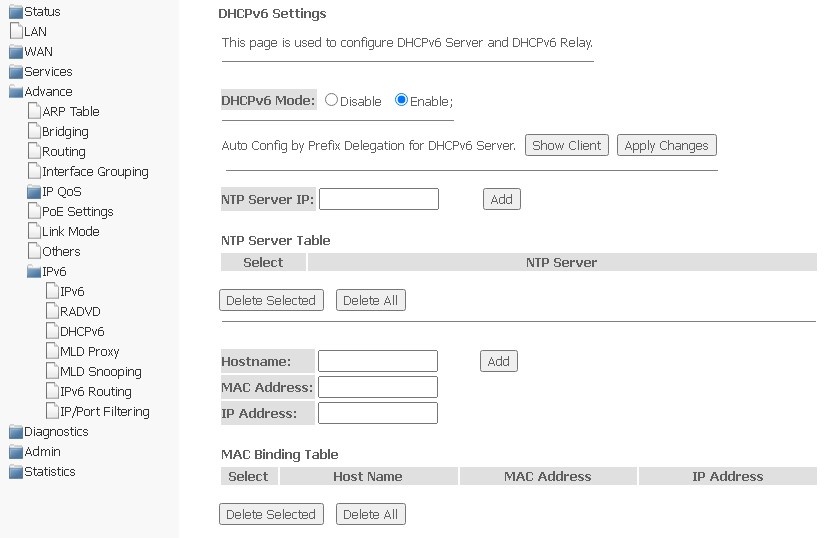
To save changes, click Apply Changes. Show Client button is used to view a table of active IP addresses of DHCPv6 server.
Advance → IPv6 → DHCPv6 → Show Client
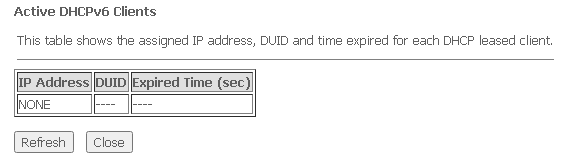
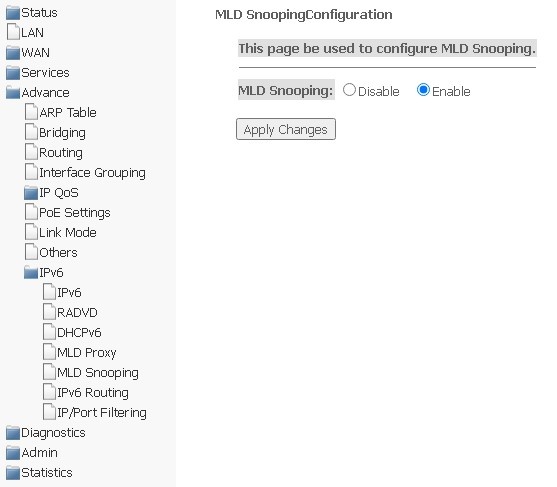
In this section, you can enable/disable the operation of the MLD-proxy; to do this, you need to select Enable or Disable.
Advance → IPv6 → MLD proxy
To save changes, click Apply Changes.
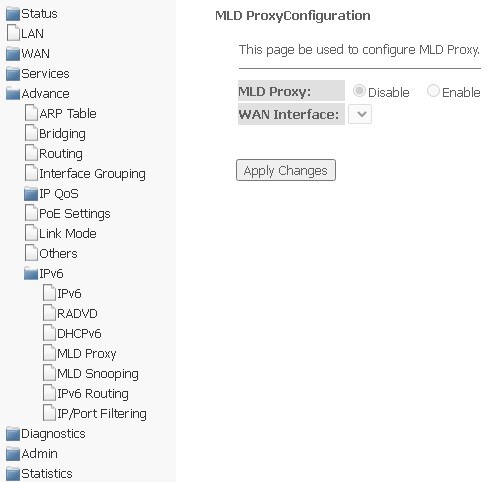
In this section, you can enable/disable MLD-snooping; to do this, you need to select Enable or Disable.
Advance → IPv6 → MLD snooping
To save changes, click Apply Changes.
Static IPv6 routes are configured in this section.
Advance → IPv6 → IPv6 routing
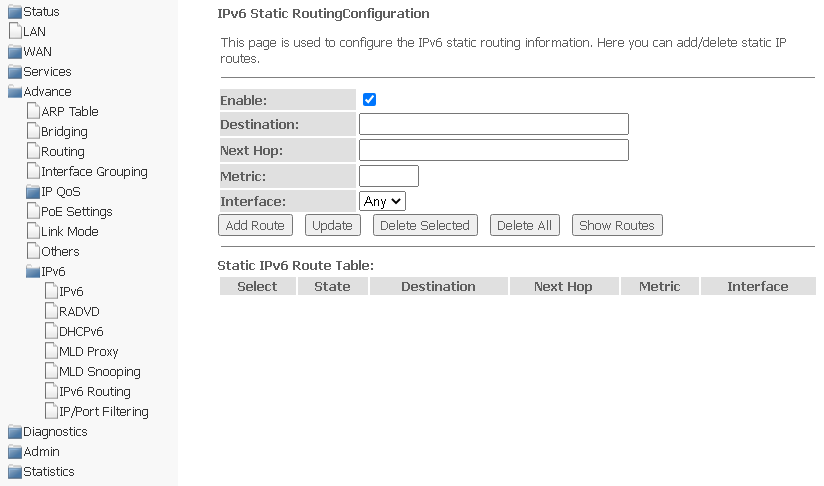
To add IPv6 routing, complete the appropriate fields and click Add Route. The added routes are displayed in Static IPv6 Route Table, to update the information, click Update. To delete the entire table, click Delete All, to delete one route, select it and click Delete Selected. The Show Routes button displays a table of static IPv6 routes that the network usually accesses.
Advance → IPv6 → IPv6 routing → Show Routes
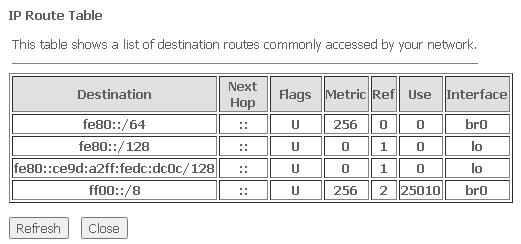
To update the table, click Refresh, to close the window — Close.
The page is used to configure filtering of data packets transmitted through the gateway.
Advance → IPv6 → IP/Port filtering
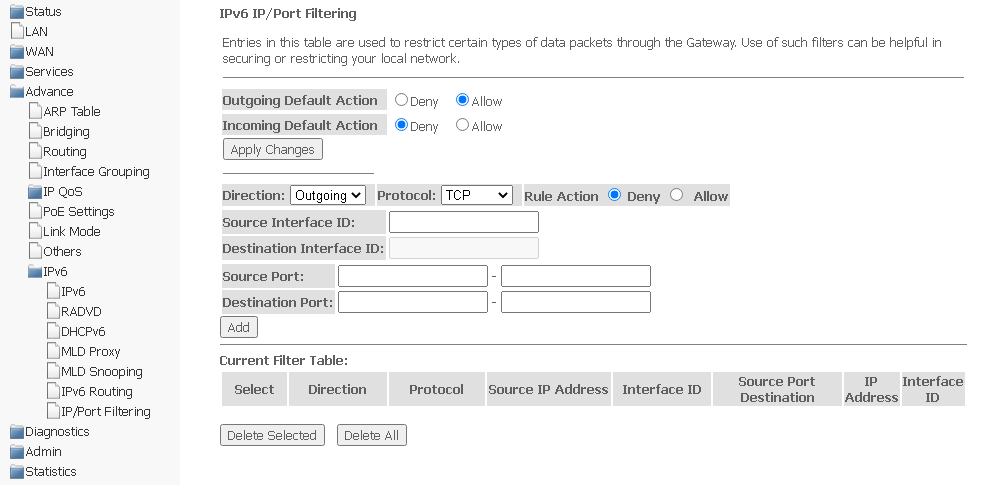
To save changes, click Apply Changes.
To add a filter, complete the appropriate fields and click Add. The added filters are displayed in Current Filter Table. To delete the entire table, click the Delete All button; to delete one filter, select it and click Delete Selected.
The section is for diagnostics of access to various network nodes.
The section is designed to check the availability of network devices using the Ping utility.
Diagnostics → Ping
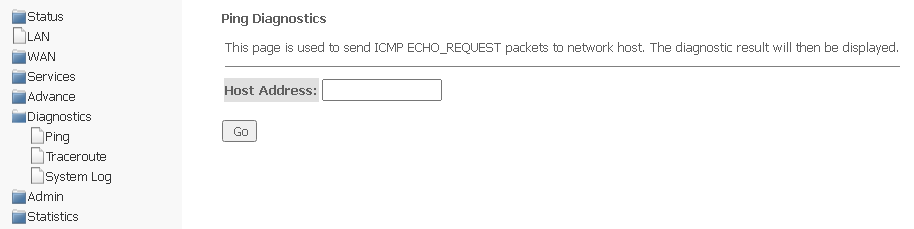
To check the availability of the connected device, enter its IP address in the Host Address field and click Go.
The section is intended for network diagnostics by sending UDP packets and receiving a message about port availability/unavailability.
Diagnostics → Traceroute
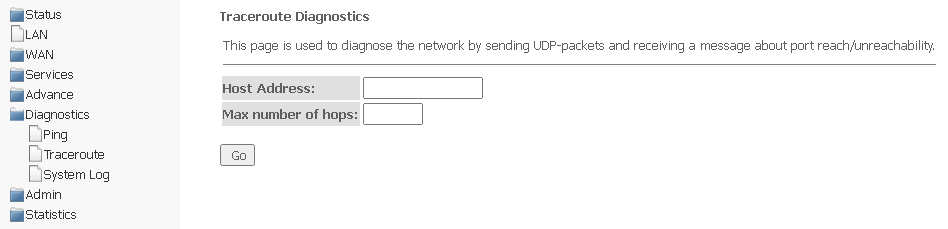
To diagnose a network, you should enter an IP address of the connected device in the Host address field and the maximum number of hops for a packet.
The section is intended for configuring/saving/viewing logging of system events. Logging can be disabled/enabled by selected Disable or Enable.
Diagnostics → System Log
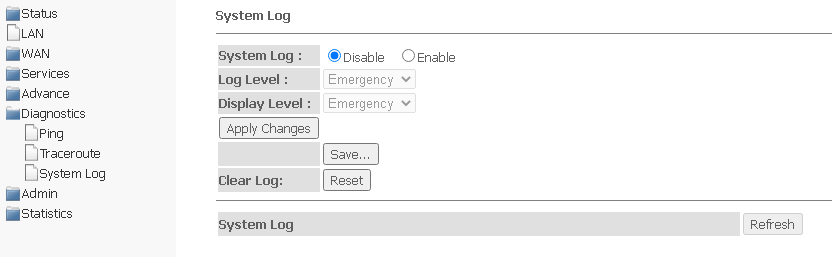
To save the log to the local storage, click the Save button.
Device management section. In this menu, passwords, time, configurations and other settings are configured.
Admin → Settings → Backup Settings
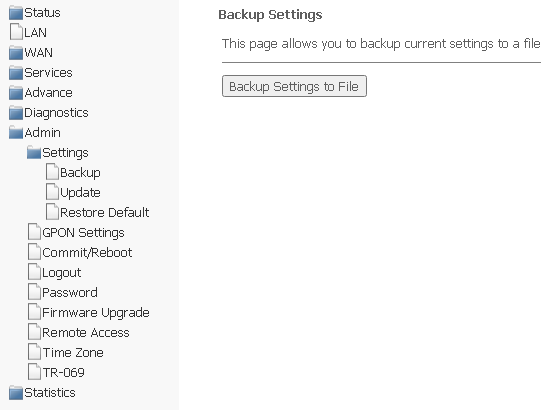
In the section, you can copy the current settings to a file (Backup Settings) by clicking Backup Settings to File.
Admin → Settings → Update Settings
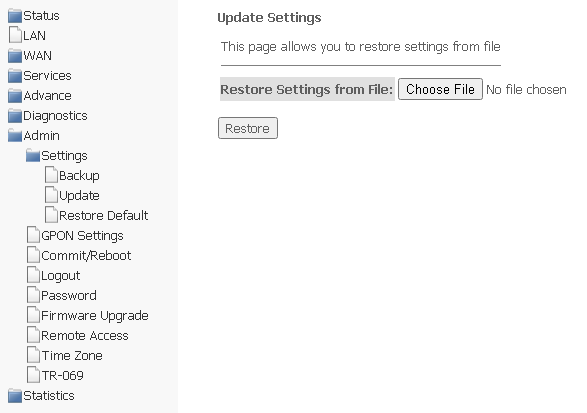
In the section, you can restore settings from a file that was saved earlier (update settings). Click Choose File to select a file, then click Restore.
Admin → Settings → Restore Default
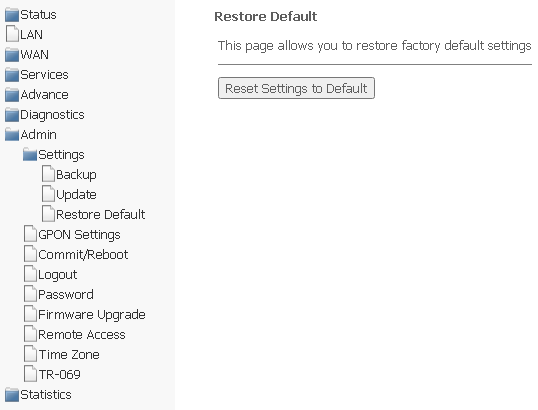
In this section, you can reset the current settings to the factory default settings (Restore Default), to do this, click Reset Settings to Default.
In this section, you can specify a password to activate the device on OLT.
Admin → GPON Setting
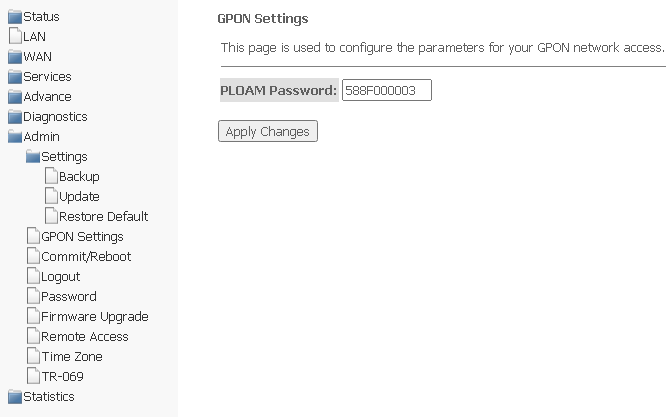
To save the changes, click Apply Changes.
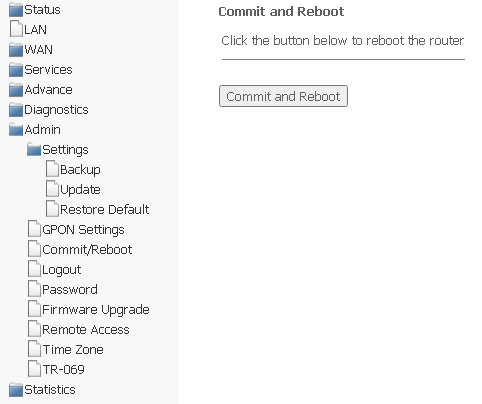
Click Commit and Reboot to reboot the device or to save changes to the system memory. It may take several minutes to restart the device.
Admin → Commit/Reboot
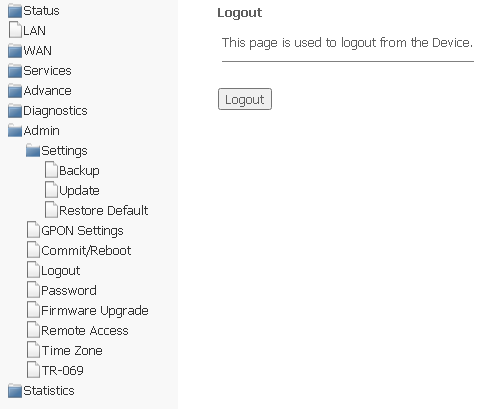
In the section it is possible to log out the account by clicking Logout.
Admin → Logout
In this section, you may change the password for access to the device.
Admin → Password
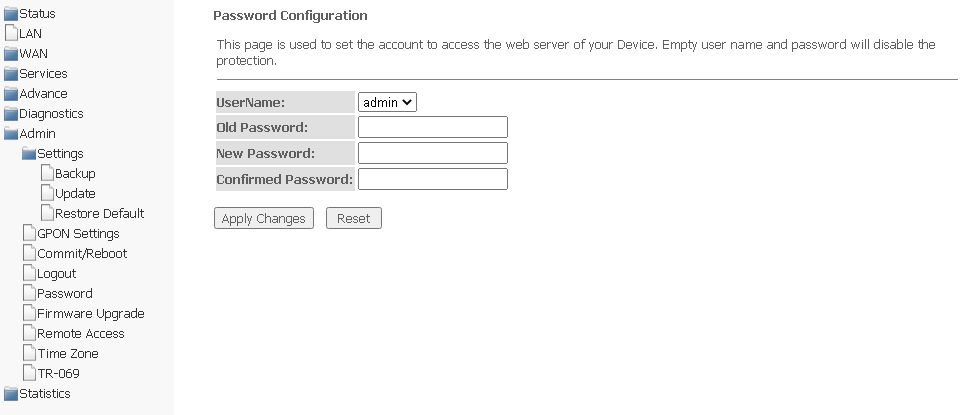
To change the password, enter the current password to the Old Password field, then the new password to New Password and to Confirmed Password.
To save changes, click Apply Changes; to reset the value, click Reset.
To update the software, select the software file using the Choose File button and click Upgrade. To reset the value, use Reset.
Admin → Firmware upgrade
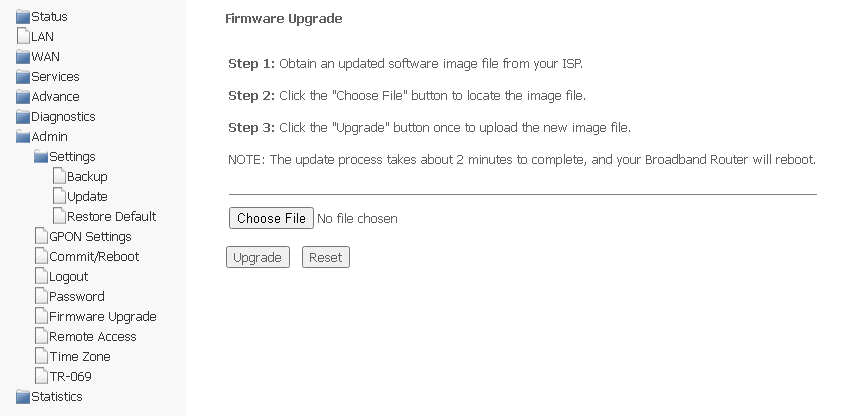
During the update process, it is not allowed to turn off the device's power or restart it. The update process may take several minutes, after which the device automatically reboots. |
In the section it is possible to configure remote access rules using HTTP/Telnet/ICMP protocols.
Admin → Remote Access
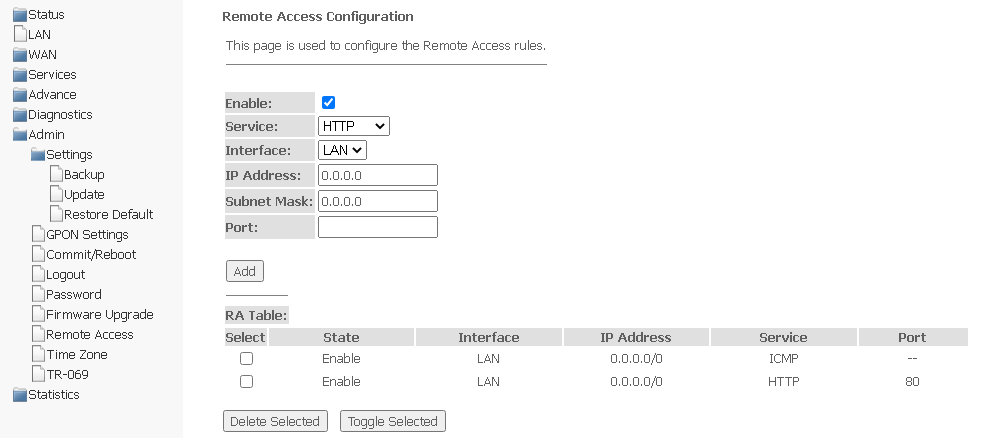
To add a rule, complete the appropriate fields and click Add. The added rules are displayed in RA Table. To activate/deactivate the selected rule, click the Toggle selected button. To delete one rule, select it in the column Select and click Delete Selected.
In this section you may configure system time, synchronization with Internet servers of the exact time is also available.
Admin → Time zone
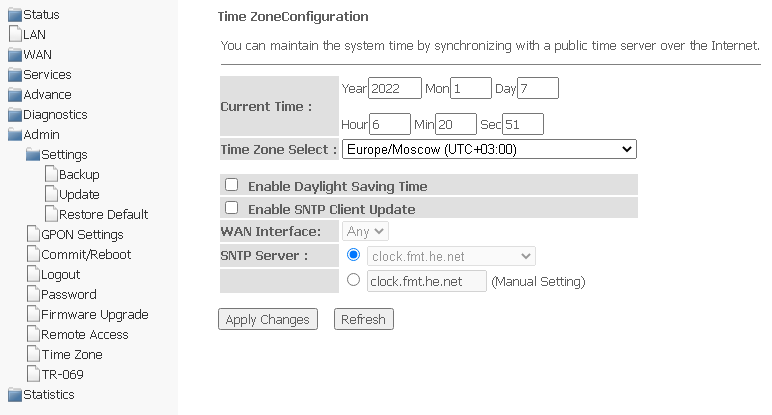
To save changes, click the "Apply Changes" button, and to update the information, click the "Refresh" button.
The section is used to specify the data for configuring the device via TR-069.
Admin → TR-069
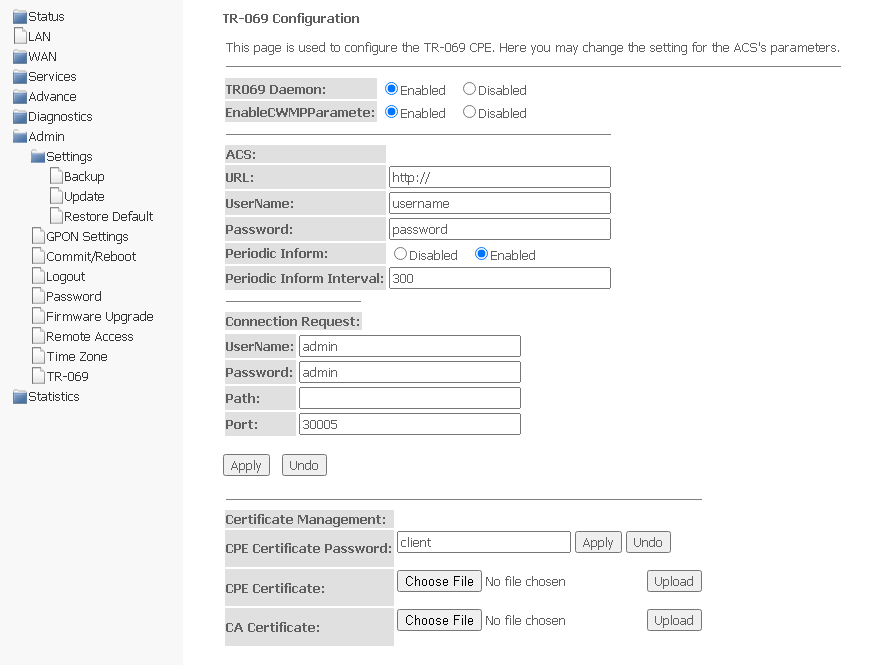
Connection Request — authorization data for connecting the server to ONT.
Certificate Management — certificate management.
To save changes, click Apply, to reset — Undo.
To upload a file, click Choose File to select a file, then click Upload.
The section displays counters/errors in packets for each interface:
Statistics → Interface
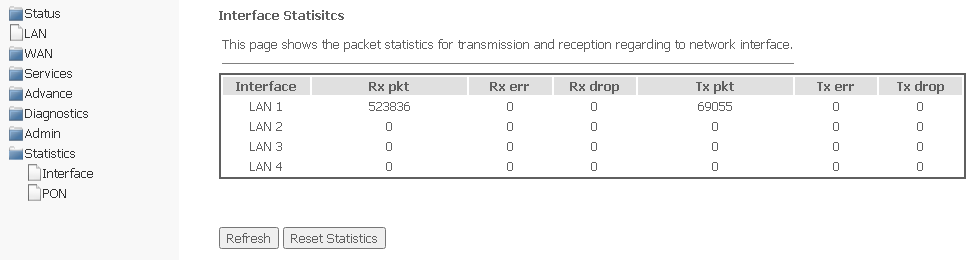
To update the data on the page, click Refresh.
The section displays counters for the optical interface:
Statistics → PON

The following statistics are available: