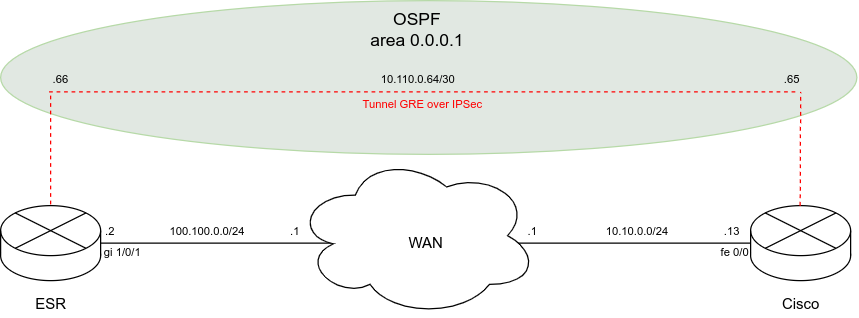
Схема:
Задача:
Настроить GRE over IPSec туннель между ESR и Cisco. На туннелях дополнительно настроить протокол динамической маршрутизации OSPF.
При настройке IPSec на ESR включен способ установления соединения ike establish-tunnel route, при таком режиме IPSec туннель поднимется при наличии транзитного трафика. Loopback интерфейсы необходимы для проверки работоспособности IPSec туннеля (передачи транзитного трафика) и в конфигурации не обязательны.
ESR:
1) Конфигурация:
esr# show running-config
router ospf log-adjacency-changes
router ospf 1
router-id 10.110.0.66
area 0.0.0.1
enable
exit
enable
exit
interface gigabitethernet 1/0/1
ip firewall disable
ip address 100.100.0.2/24
exit
interface loopback 1
ip address 2.2.2.2/32
exit
tunnel gre 1
mtu 1476
ip firewall disable
local address 100.100.0.2
remote address 10.10.0.13
ip address 10.110.0.66/30
ip ospf instance 1
ip ospf area 0.0.0.1
ip ospf
enable
exit
security ike proposal IKEPROP
encryption algorithm aes128
dh-group 2
exit
security ike policy IKEPOL
lifetime seconds 86400
pre-shared-key ascii-text encrypted 8CB5107EA7005AFF
proposal IKEPROP
exit
security ike gateway IKEGW
ike-policy IKEPOL
local address 100.100.0.2
local network 100.100.0.2/32 protocol gre
remote address 10.10.0.13
remote network 10.10.0.13/32 protocol gre
mode policy-based
exit
security ipsec proposal IPPROP
encryption algorithm aes128
exit
security ipsec policy IPPOL
proposal IPPROP
exit
security ipsec vpn IPSEC
mode ike
ike establish-tunnel route
ike gateway IKEGW
ike ipsec-policy IPPOL
enable
exit
ip route 0.0.0.0/0 tunnel gre 1
ip route 10.10.0.0/24 100.100.0.1
2) Информация о состоянии протокола OSPF и IPSec туннеля:
esr# show ip ospf neighbors Router ID Pri State DTime Interface Router IP --------- --- ----- ----- ----------------- --------- 10.110.0.65 1 Full/BDR 00:35 gre 1 10.110.0.65 esr# show security ipsec vpn status IPSEC Currently active IKE SA: Name: IPSEC State: Established Version: v1-only Unique ID: 3 Local host: 100.100.0.2 Remote host: 10.10.0.13 Role: Initiator Initiator spi: 0x15dc63f5881abbb0 Responder spi: 0xd45e86e5abb121d9 Encryption algorithm: des Authentication algorithm: sha1 Diffie-Hellman group: 2 Established: 12 minutes and 34 seconds ago Rekey time: 12 minutes and 34 seconds Reauthentication time: 23 hours, 32 minutes and 7 seconds Child IPsec SAs: Name: IPSEC State: Installed Protocol: esp Mode: Tunnel Encryption algorithm: aes128 Authentication algorithm: sha1 Rekey time: 32 minutes Life time: 47 minutes and 26 seconds Established: 12 minutes and 34 seconds ago Traffic statistics: Input bytes: 540 Output bytes: 540 Input packets: 5 Output packets: 5
Cisco:
1) Конфигурация:
crypto isakmp policy 2 encr aes authentication pre-share group 2 crypto isakmp key password address 100.100.0.2 ! crypto ipsec security-association lifetime seconds 86400 ! crypto ipsec transform-set strong esp-aes esp-sha-hmac ! crypto map mymap local-address FastEthernet0/0 crypto map mymap 119 ipsec-isakmp set peer 100.100.0.2 set transform-set strong match address 119 ! ! interface Loopback1 ip address 1.1.1.1 255.255.255.255 ! ! interface Tunnel2 ip address 10.110.0.65 255.255.255.252 ip ospf 1 area 0.0.0.1 tunnel source 10.10.0.13 tunnel destination 100.100.0.2 ! ! interface FastEthernet0/0 ip address 10.10.0.13 255.255.255.0 duplex auto speed auto crypto map mymap ! router ospf 1 router-id 10.110.0.65 log-adjacency-changes ! ip route 100.100.0.0 255.255.255.0 10.10.0.1 ip route 0.0.0.0 0.0.0.0 Tunnel2 ! access-list 119 permit gre host 10.10.0.13 host 100.100.0.2
2) Информация о состоянии протокола OSPF и IPSec туннеля:
Router#show ip ospf neighbor
Neighbor ID Pri State Dead Time Address Interface
10.110.0.66 0 FULL/ - 00:00:32 10.110.0.66 Tunnel2
Router#show crypto ipsec sa
interface: FastEthernet0/0
Crypto map tag: mymap, local addr 10.10.0.13
protected vrf: (none)
local ident (addr/mask/prot/port): (10.10.0.13/255.255.255.255/47/0)
remote ident (addr/mask/prot/port): (100.100.0.2/255.255.255.255/47/0)
current_peer 100.100.0.2 port 500
PERMIT, flags={origin_is_acl,}
#pkts encaps: 5, #pkts encrypt: 5, #pkts digest: 5
#pkts decaps: 5, #pkts decrypt: 5, #pkts verify: 5
#pkts compressed: 0, #pkts decompressed: 0
#pkts not compressed: 0, #pkts compr. failed: 0
#pkts not decompressed: 0, #pkts decompress failed: 0
#send errors 0, #recv errors 0
local crypto endpt.: 10.10.0.13, remote crypto endpt.: 100.100.0.2
path mtu 1500, ip mtu 1500, ip mtu idb FastEthernet0/0
current outbound spi: 0xC9A1F292(3382833810)
PFS (Y/N): Y, DH group: group2
inbound esp sas:
spi: 0x7783E2D2(2005131986)
transform: esp-aes esp-sha-hmac ,
in use settings ={Tunnel, }
conn id: 2001, flow_id: FPGA:1, sibling_flags 80000046, crypto map: mymap
sa timing: remaining key lifetime (k/sec): (4480312/3033)
IV size: 16 bytes
replay detection support: Y
Status: ACTIVE
inbound ah sas:
inbound pcp sas:
outbound esp sas:
spi: 0xC9A1F292(3382833810)
transform: esp-aes esp-sha-hmac ,
in use settings ={Tunnel, }
conn id: 2002, flow_id: FPGA:2, sibling_flags 80000046, crypto map: mymap
sa timing: remaining key lifetime (k/sec): (4480312/3033)
IV size: 16 bytes
replay detection support: Y
Status: ACTIVE
outbound ah sas:
outbound pcp sas: