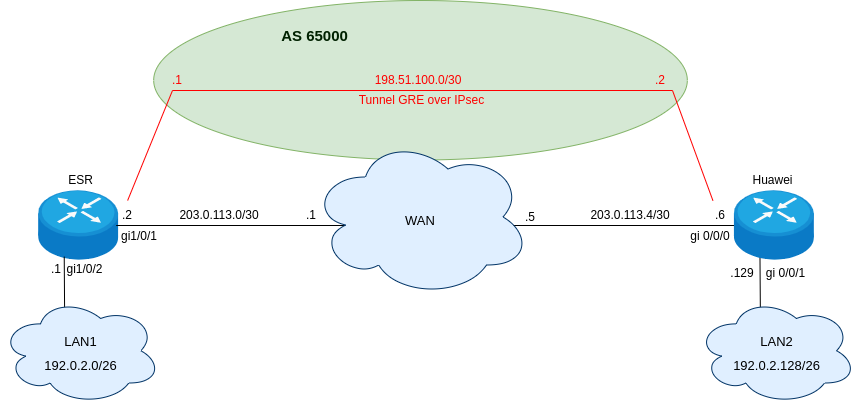
Схема:
Задача: Настроить GRE over IPSec туннель между ESR и Huawei. Также необходимо настроить протокол динамической маршрутизации BGP между туннельными адресами для анонсирования локальных подсетей.
1. Конфигурации устройств
Пример конфигурации ESR:
ESR# show running-config hostname ESR
router bgp log-neighbor-changesrouter bgp 65000 router-id 198.51.100.1 neighbor 198.51.100.2 remote-as 65000 address-family ipv4 unicast enable exit enable exit address-family ipv4 unicast network 192.0.2.0/26 exit enableexit
interface gigabitethernet 1/0/1 ip firewall disable ip address 203.0.113.2/30exitinterface gigabitethernet 1/0/2 ip firewall disable ip address 192.0.2.1/26exittunnel gre 1 ttl 255 mtu 1400 ip firewall disable local address 203.0.113.2 remote address 203.0.113.6 ip address 198.51.100.1/30 enableexit
security ike proposal ike_proposal authentication algorithm sha1 encryption algorithm aes128 dh-group 2exit
security ike policy ike_policy pre-shared-key ascii-text Password_123 proposal ike_proposalexit
security ike gateway ike_gateway ike-policy ike_policy local address 203.0.113.2 local network 203.0.113.2/32 protocol gre remote address 203.0.113.6 remote network 203.0.113.6/32 protocol gre mode policy-basedexit
security ipsec proposal ipsec_proposal authentication algorithm sha1 encryption algorithm aes128 protocol espexit
security ipsec policy ipsec_policy proposal ipsec_proposalexit
security ipsec vpn ipsec_vpn mode ike type transport ike establish-tunnel route ike gateway ike_gateway ike ipsec-policy ipsec_policy enableexit
ip route 203.0.113.4/30 203.0.113.1
Пример конфигурации Huawei:
[Huawei]display current-configuration ...#ipsec proposal 1 encapsulation-mode transport esp authentication-algorithm sha1 esp encryption-algorithm aes-128 #...ike proposal 1 encryption-algorithm aes-128 dh group2 authentication-algorithm sha1 sa duration 10800 authentication-method pre-share integrity-algorithm hmac-sha1-96 prf hmac-sha1 #ike peer ike_peer pre-shared-key simple Password_123 ike-proposal 1 local-address 203.0.113.6 remote-address authentication-address 203.0.113.2
ikev1 phase1-phase2 sa dependent#ipsec profile ipsec_profile ike-peer ike_peer proposal 1 sa duration traffic-based 0 sa duration time-based 3600#
...
#interface GigabitEthernet0/0/0 ip address 203.0.113.6 255.255.255.252#interface GigabitEthernet0/0/1 ip address 192.0.2.129 255.255.255.192#interface Tunnel0/0/0 mtu 1400 tcp adjust-mss 1360 ip address 198.51.100.2 255.255.255.252 tunnel-protocol gre source 203.0.113.6 destination 203.0.113.2 ipsec profile ipsec_profile#bgp 65000 router-id 198.51.100.2 peer 198.51.100.1 as-number 65000 # ipv4-family unicast undo synchronization network 192.0.2.128 255.255.255.192 peer 198.51.100.1 enable
#
...
#
ip route-static 203.0.113.2 255.255.255.255 203.0.113.5
...
2. Оперативный вывод команд статуса IPsec-туннеля, BGP-сессии, полученной от BGP-соседа маршрутной информации, а также проверка IP-связанности с удаленными локальными подсетями.
Оперативный вывод команд с ESR:
ESR# show security ipsec vpn status ipsec_vpn Currently active IKE SA: Name: ipsec_vpn State: Established Version: v1-only Unique ID: 2 Local host: 203.0.113.2 Remote host: 203.0.113.6 Role: Initiator Initiator spi: 0xa7c8949a175d688c Responder spi: 0x083da58456a8aeee Encryption algorithm: aes128 Authentication algorithm: sha1 Diffie-Hellman group: 2 Established: 1 minute and 22 seconds ago Rekey time: 1 minute and 22 seconds Reauthentication time: 2 hours, 49 minutes and 8 seconds Child IPsec SAs: Name: ipsec_vpn-2 State: Installed Protocol: esp Mode: Transport Encryption algorithm: aes128 Authentication algorithm: sha1 Rekey time: 47 minutes and 11 seconds Life time: 58 minutes and 38 seconds Established: 1 minute and 22 seconds ago Traffic statistics: Input bytes: 994 Output bytes: 1127 Input packets: 13 Output packets: 16 -------------------------------------------------------------
ESR# show bgp neighbors BGP neighbor is 198.51.100.2 BGP state: Established Type: Static neighbor Neighbor address: 198.51.100.2 Neighbor AS: 65000 Neighbor ID: 198.51.100.2 Neighbor caps: refresh AS4 Session: internal multihop AS4 Source address: 198.51.100.1 Weight: 0 Hold timer: 109/180 Keepalive timer: 15/60 Address family ipv4 unicast: Send-label: No Default originate: No Default information originate: No Uptime: 87 s
ESR# show ip route bgp Status codes: u - unicast, b - broadcast, m - multicast, a - anycast * - valid, > - bestOrigin codes: i - IGP, e - EGP, ? - incomplete
Network Next Hop Metric LocPrf Weight Path *> u 192.0.2.128/26 198.51.100.2 0 100 0 i
ESR# ping 192.0.2.129PING 192.0.2.129 (192.0.2.129) 56 bytes of data.!!!!!--- 192.0.2.129 ping statistics ---5 packets transmitted, 5 received, 0% packet loss, time 4005msrtt min/avg/max/mdev = 0.829/1.387/2.785/0.723 ms
Оперативный вывод команд с Huawei:
[Huawei]display ipsec sa
ipsec sa information:
===============================Interface: Tunnel0/0/0===============================
----------------------------- IPSec profile name: "ipsec_profile" Mode : PROF-ISAKMP ----------------------------- Connection ID : 65 Encapsulation mode: Transport Holding time : 0d 0h 2m 35s Tunnel local : 203.0.113.6/500 Tunnel remote : 203.0.113.2/500 Flow source : 203.0.113.6/255.255.255.255 47/0-65535 Flow destination : 203.0.113.2/255.255.255.255 47/0-65535
[Outbound ESP SAs] SPI: 3315963714 (0xc5a59742) Proposal: ESP-ENCRYPT-AES-128 ESP-AUTH-SHA1 SA remaining soft duration (kilobytes/sec): 0/685 SA remaining hard duration (kilobytes/sec): 0/1045 Outpacket count : 20 Outpacket encap count : 20 Outpacket drop count : 0 Max sent sequence-number: 20 UDP encapsulation used for NAT traversal: N
[Inbound ESP SAs] SPI: 5425586 (0x52c9b2) Proposal: ESP-ENCRYPT-AES-128 ESP-AUTH-SHA1 SA remaining soft duration (kilobytes/sec): 0/685 SA remaining hard duration (kilobytes/sec): 0/1045 Inpacket count : 22 Inpacket decap count : 22 Inpacket drop count : 0 Max received sequence-number: 23 UDP encapsulation used for NAT traversal: N Anti-replay : Enable Anti-replay window size: 1024
[Huawei]display bgp peer
Status codes: * - Dynamic
BGP local router ID : 198.51.100.2 Local AS number : 65000 Total number of peers : 1 Peers in established state : 1 Total number of dynamic peers : 0
Peer V AS MsgRcvd MsgSent OutQ Up/Down State PrefRcv
198.51.100.1 4 65000 7 7 0 00:03:10 Established 1
[Huawei]display bgp routing-table
BGP Local router ID is 198.51.100.2 Status codes: * - valid, > - best, d - damped, h - history, i - internal, s - suppressed, S - Stale Origin : i - IGP, e - EGP, ? - incomplete
Total Number of Routes: 2 Network NextHop MED LocPrf PrefVal Path/Ogn
*>i 192.0.2.0/26 198.51.100.1 100 0 i *> 192.0.2.128/26 0.0.0.0 0 0 i
[Huawei]ping 192.0.2.1 PING 192.0.2.1: 56 data bytes, press CTRL_C to break Reply from 192.0.2.1: bytes=56 Sequence=1 ttl=64 time=1 ms Reply from 192.0.2.1: bytes=56 Sequence=2 ttl=64 time=1 ms Reply from 192.0.2.1: bytes=56 Sequence=3 ttl=64 time=1 ms Reply from 192.0.2.1: bytes=56 Sequence=4 ttl=64 time=1 ms Reply from 192.0.2.1: bytes=56 Sequence=5 ttl=64 time=1 ms
--- 192.0.2.1 ping statistics --- 5 packet(s) transmitted 5 packet(s) received 0.00% packet loss round-trip min/avg/max = 1/1/1 ms